Search the Community
Showing results for tags 'bitlocker encryption'.
-
We use SCCM to enable/configure BitLocker on Windows 10 computers. The BitLocker PIN must follow our password policy for changing the password every 60 days. We don't see that as a selection when configuring the policy. Can this be done?
- 3 replies
-
- sccm 2103
- bitlocker encryption
-
(and 1 more)
Tagged with:
-
Hi all, I'm configuring a lab here for SCCm 2002 and I am looking at implementing bitlocker. I have been reading that from 2002, we don't need to enable https through out the MP to encrypt the recovery keys, we can just enable it on IIS. The problem I have is I have no idea how to do this. I quote Niall here from another post: "if you choose to not use PKI in your infrastructure then you need to add a PKI-based server auth cert to the IIS website hosting the recovery service – this can be the same cert you used when configuring HTTPS on the MP or another PKI-issued cert if not using HTTPS." , but again I have no idea how to get to it. If someone could show me where in IIS I am "hosting" said recovery keys, that would really be appreciated. I have enable bitlocker management, created a policy, and selected 'enable plain text recovery keys". Now it seems I cannot create another policy without plain text recovery keys. My primary concern however is know how and where I can "host" recovery keys on IIS. I have uploaded a screenshot from my lab here an I hope this helps someone as I do not know what I need to do here. Thanks again.
-
Hi There, Anyone here has hands-on experience on implement Bit-Locker To-Go? In my environment we use SCCM CB-1902 and MBAM server & client. We have single drive in all the client and it has been protected using MBAM agent. Now looking for encryption the removal disc \USB automatically, when it insert. How can I achieve this? Please free to ask me, if required more information. BR, Biju
-
- bitlocker
- bitlocker encryption
-
(and 4 more)
Tagged with:
-
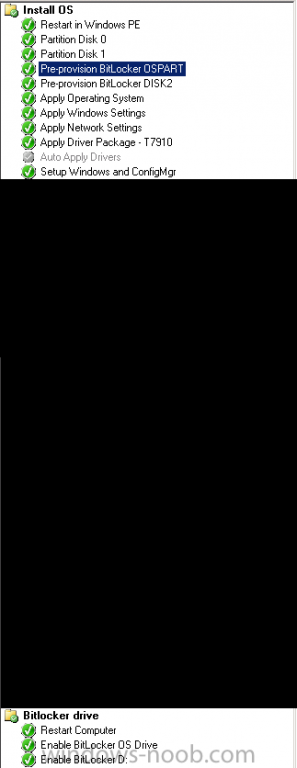
Hi all, Before I start off. This is a best-practice type of question. The situation below works but I'm unhappy because I need to enable the Continue on Error option for it to work and I was wondering if anyone has a better way of achieving my goals. In our organization we normally have 1 disk per system, be it workstation or laptop. All systems are Bitlockered during OSD. This week we purchased 2 new workstations however with 2 disks: 1 500GB SSD (Boot, OS - disk 0) and 1 2TB HDD (disk 1). I built a TS for OSD. Tweaked some steps for Bitlocker. Ran OSD. Crashed and burned. Status so far: - Pre-provisioning works for disk 0 and disk 1 - Bitlocker fails to encrypt disk 1 The failure code is : 0x000000FF (255) Log file and a screenshot of the TS are included. Short explanation of the TS. - Disk 0 is partitioned with a 300MB bootpart and remaining space is the OS partition. The latter receives variable: OSPART - Disk 1 is 1 partition, variable: DISK2 - @ Enable Bitlocker OS drive has the following options: Current OS drive, TPM only, ADDS backup, wait for BL to complete... - @ Enable Bitlocker D: Specific drive: D:, ADDS backup, wait for BL to complete... The step that fails (oddly) is the Enable BL OS Drive step, with the following message: Failed to run the action: Enable BitLocker OS Drive. The extended attributes are inconsistent. (Error: 000000FF; Source: Windows) TSManager 29-May-2015 11:58:29 3836 (0x0EFC). If you then boot to OS the funny thing you find is that the failure results in the OS drive being fully encrypted but the other disk has BL suspended. So technically it fails to encrypt the other disk. When the Continue on Error option is ticked at the Enable BL OS drive step: All good! Everything is encypted as it should be. Please have a look at the excerpt of the smsts.log and if anyone has any ideas: I'm all ears. BL.log
- 5 replies
-
- bitlocker pre-provision
- bitlocker encryption
-
(and 2 more)
Tagged with: