Search the Community
Showing results for tags 'bit locker'.
-
Hi There, Anyone here has hands-on experience on implement Bit-Locker To-Go? In my environment we use SCCM CB-1902 and MBAM server & client. We have single drive in all the client and it has been protected using MBAM agent. Now looking for encryption the removal disc \USB automatically, when it insert. How can I achieve this? Please free to ask me, if required more information. BR, Biju
-
- bitlocker
- bitlocker encryption
-
(and 4 more)
Tagged with:
-
I am testing what happens when users enter their bitlocker PIN wrong too many times, but cannot find a way to access the password to unlock the TPM. I believe all that is visible is a hash of it. Does anyone have any info on this? At the moment, all i can do is leave the computer logged in with recovery key and left active until the TPM reset period passes.
-
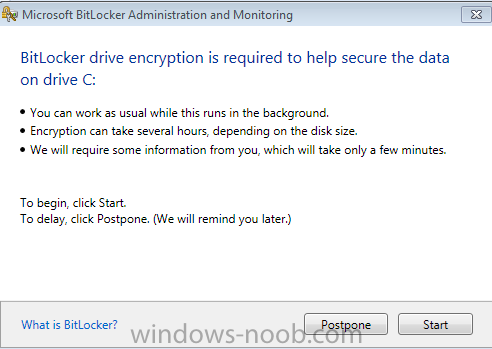
Currently I am in the process of testing out the GPO settings including a pilot group of users for MDOP MBAM Bitlocker encryption. The only question I have is how do you suppress that box where it ask for Postpone/Start; (below image). I am doing this on machines who already have Windows 7 and deployed without Bitlocker enabled. First project was XP -> Windows 7 migrations. Now we are circling back around enabling Bitlocker on existing machines. All clients have MDOP MBAM 2.0 installed already. Everything works as I have intended, but with Postpone and Start GUI popping up to initiate it from the user. So we are looking to have it without any user interactions soon as Policy kicks in, so forth. I did try using the supplied regkey template in C:\Program Files\Microsoft\MDOP MBAM but I can't figure out what keys to add/remove, if any that could run without user interaction. Adding NoStartDelay DWORD doesn't seem to do anything other than display the pop-up sooner than the default 90 minute random cycle. Any suggestions is greatly appreciated. Eric Lenovo Shop - Desktops/Laptops 2000+ nodes - Windows 7 x64-bit SCCM 2012 (non-SP/CU) MBAM Server v.2.0 (non-SP1) - Stand-alone configuration with SQL
- 3 replies
-
- bit locker
- windows 7
-
(and 3 more)
Tagged with:
-
Hi All, I have searched high and low, non-stop for days trying to find an answer. I have finally admitted defeat because I am unable to find the information "out there", as I can normally find "anything" within minutes of searching and so after 3 days, it's fair to say I have been unsuccessful. Task 1: Create a regular task sequence to install my OS image. My task sequence is very generic and is built from the default structure/template assigned by the wizard when installing an image package TS. The task sequence works perfectly fine when a machine PXE boots and the respective TS is selected. The process goes from end to end, and results with an install OS that uses my unattend.xml to make the operation as lite touch as possible. The only drive (C:) is bitlocked in the process by design. Everything is great so far! Task 2: Create a USB Media of the Task Sequence I have a requirement to port this over to a USB pen drive. Using the "Create Task Sequence Media" wizard, I built a USB pen drive. I tested it by booting from the pen drive on physical hardware, and watched the process all the way through. There were NO errors - perfect! Then I shortly realised that when I removed the USB pen drive and started up the computer, I got the Bitlocker Drive Encryption Password Entry screen. The computer had encrypted with the assumption that my USB pen drive was a part of the hardware, and so when it was removed, it believes the hardware had changed. I had to insert the USB pen drive in order to boot the computer to Windows, and only then could I remove the USB pen drive. Problem/Question: What do I need to do to bypass/ignore the USB Media being apart of the hardware? My thoughts were: Method 1: implement a script that forces the user to eject/remove the USB pen drive at a specific step in the TS so that the sequence will continue and bitlocker the hard disk, and since there is no USB pen drive present at this time, everything should be OK. Concerns: I have written a script that will not "finish/exit" unless the USB drives are all empty and do not contain any mass storage devices. My concerns are that once the USB has been removed, I would assume an error would occur because the USB media is missing here on and it can not be read from. How do I overcome this - is this the right thought process? Method 2: Script the bit locker step so that it totally ignores the USB drive when encrypting. Concerns: I don't know how to tell bit locker to ignore the USB pen drive (baring in mind that the USB drive letter could vary depending on the specs of the hardware it is inserted into). Also, encrypting the USB drive is not the actual problem because that doesn't happen (only the C: drive is encrypted), the problem is that the system appears to think the USB pen drive is part of the physical machine. As I have said, I've been hurting my brain for days now to get at least some guidance on this, and I've come up with nothing. This must have been done before by *someone, somewhere*, right? Any advice or tips are appreciated - but better yet, if anyone has first hand experience of doing this, I would love to hear from you. Thanks, WizzKidd
-
We've got several laptops that we've had to re-image due to a virus, where the hard drive had been encrypted by bit locker. These are all Lenovo laptops, a few different models, and they all use the TPM chip. We couldn't un-encrypt the drive before we re-imaged, but we did use diskpart to remove all partitions and clean the disk. We even tried using a new disk right out of the package. We also turned off the TPM through BIOS. During the imaging, it gets to applying the OS image, 1-4 squares, then errors out with an 80070241 error. Upon checking the SMSTS logs, I get a different error each time I try. Here is one of the erros: Failed to save environment to (80070057) TSManager 11/30/2011 7:16:58 PM 1328 (0x0530) Failed to save the current environment block. This is usually caused by a problem with the program. Please check the Microsoft Knowledge Base to determine if this is a known issue or contact Microsoft Support Services for further assistance. The parameter is incorrect. (Error: 80070057; Source: Windows)Failed to persist execution state. Error 0x(80070057) TSManager 11/30/2011 7:16:58 PM 1328 (0x0530) Failed to save execution state and environment to local hard disk I tried to get some other errors I had seen in the past, but couldn't reproduce them. I'm hoping someone here has seen this problem and can give me some ideas on what to try. I will try to get more logs, but now some of them are coming up without any errors in them.
- 1 reply
-
- Bit Locker
- 80070057
-
(and 1 more)
Tagged with: