Search the Community
Showing results for tags 'enrollment'.
-
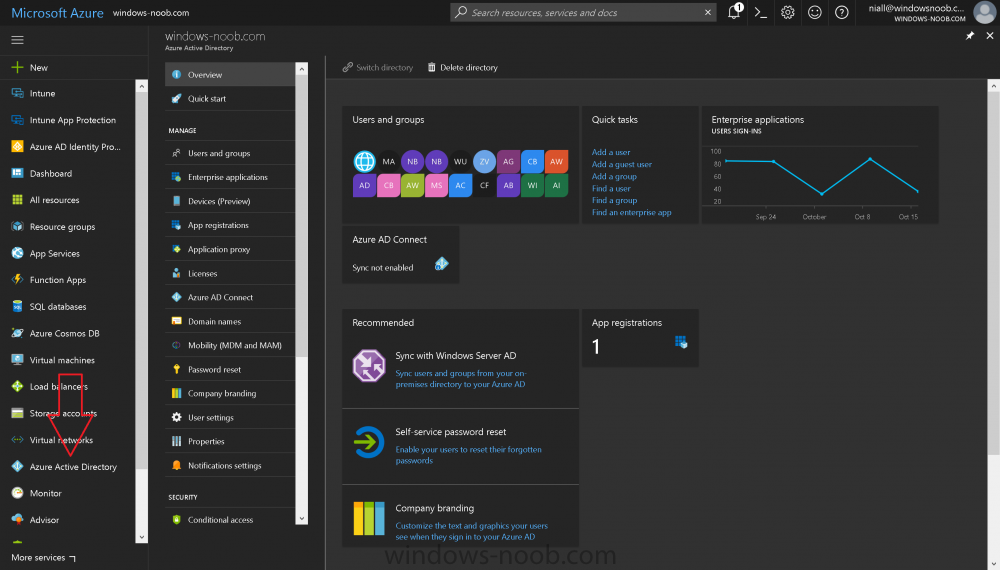
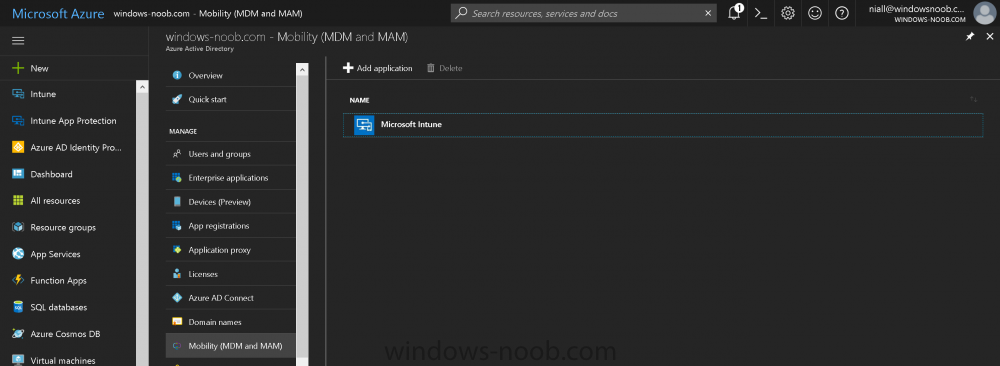
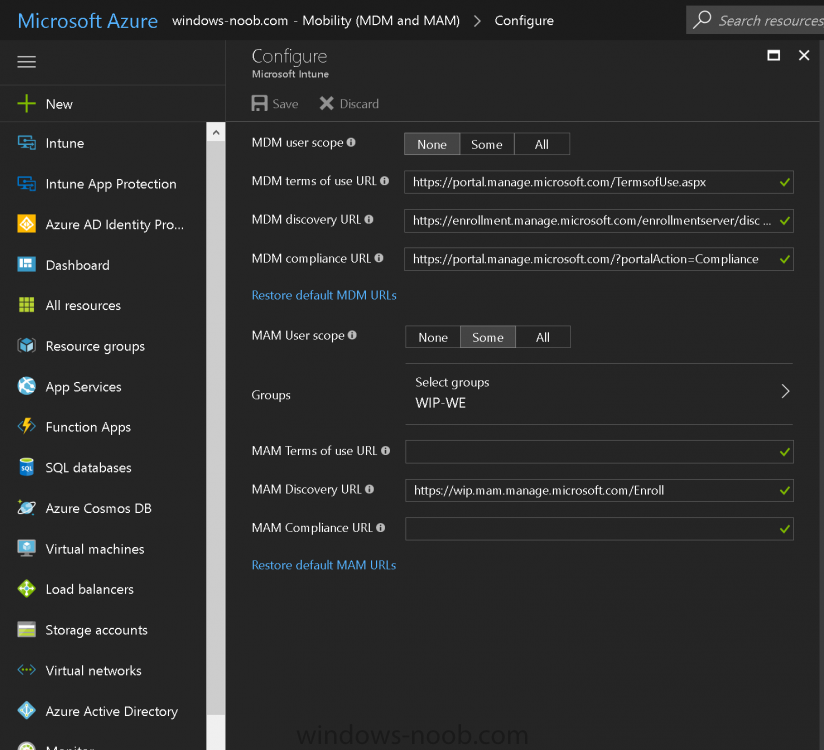
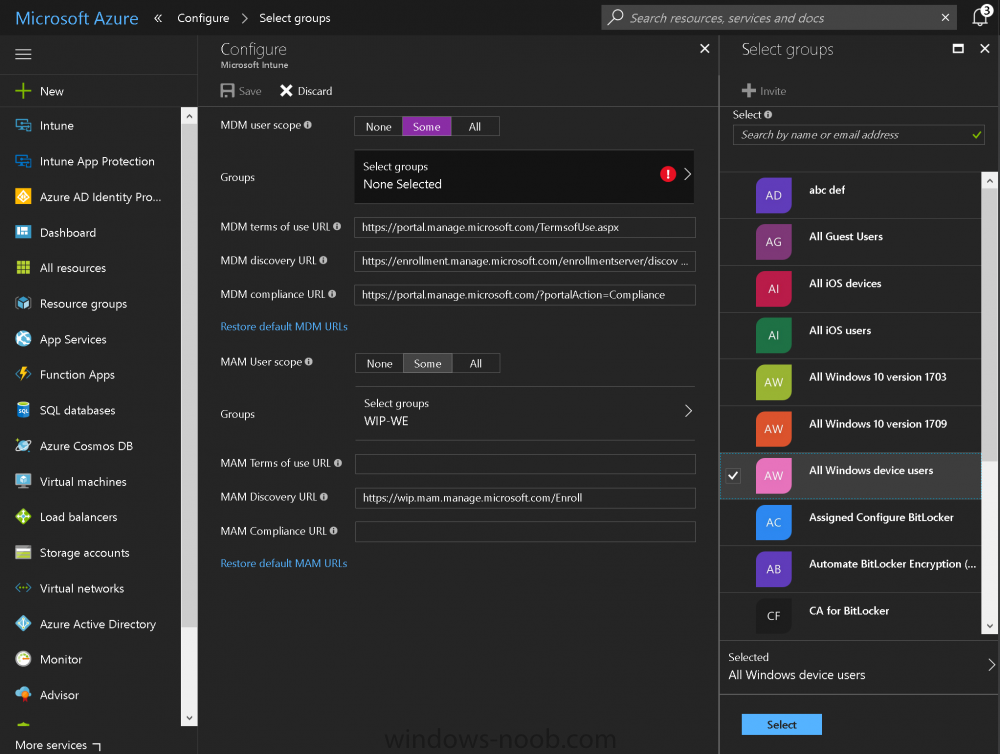
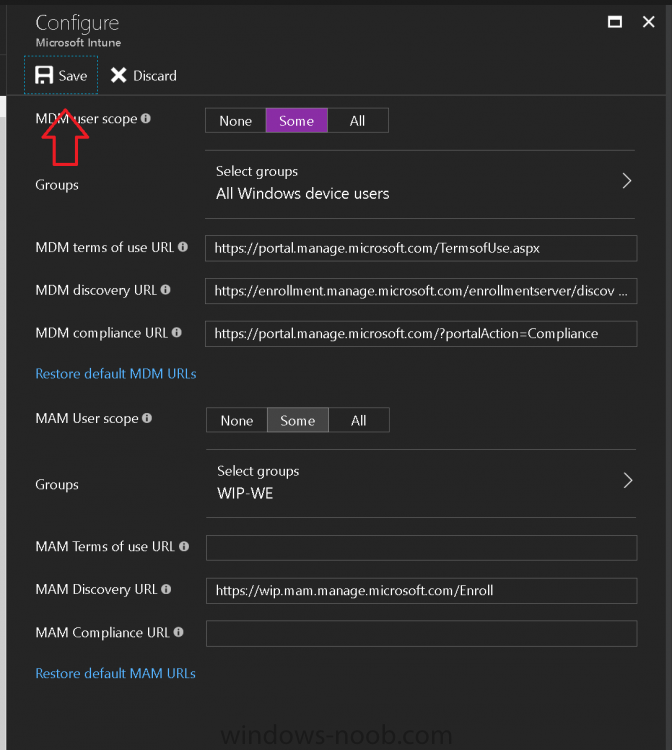
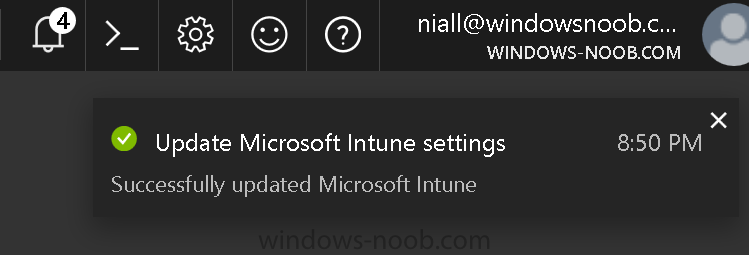
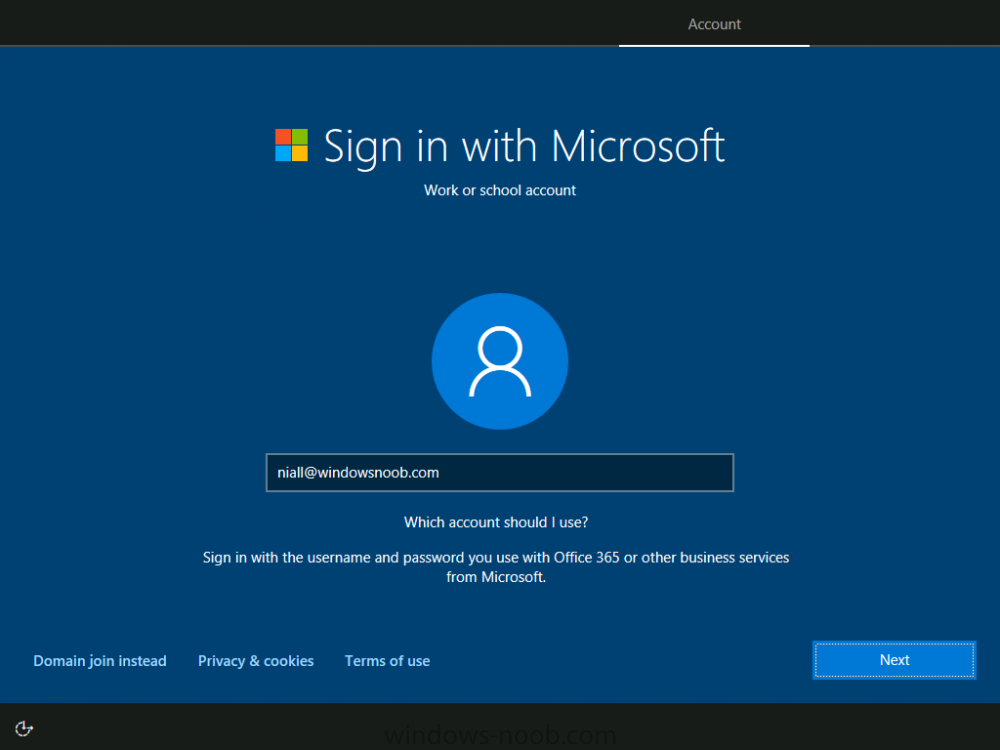
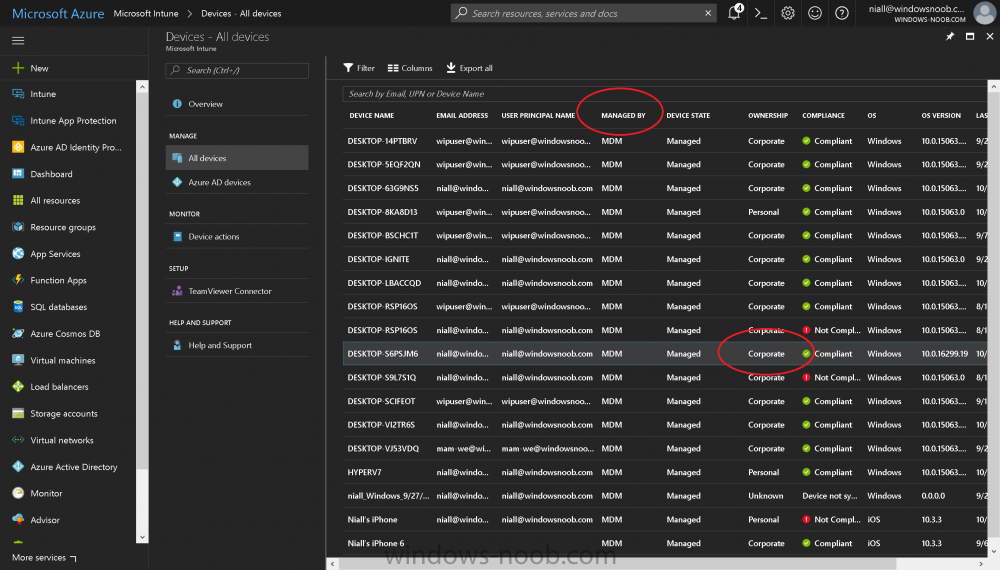
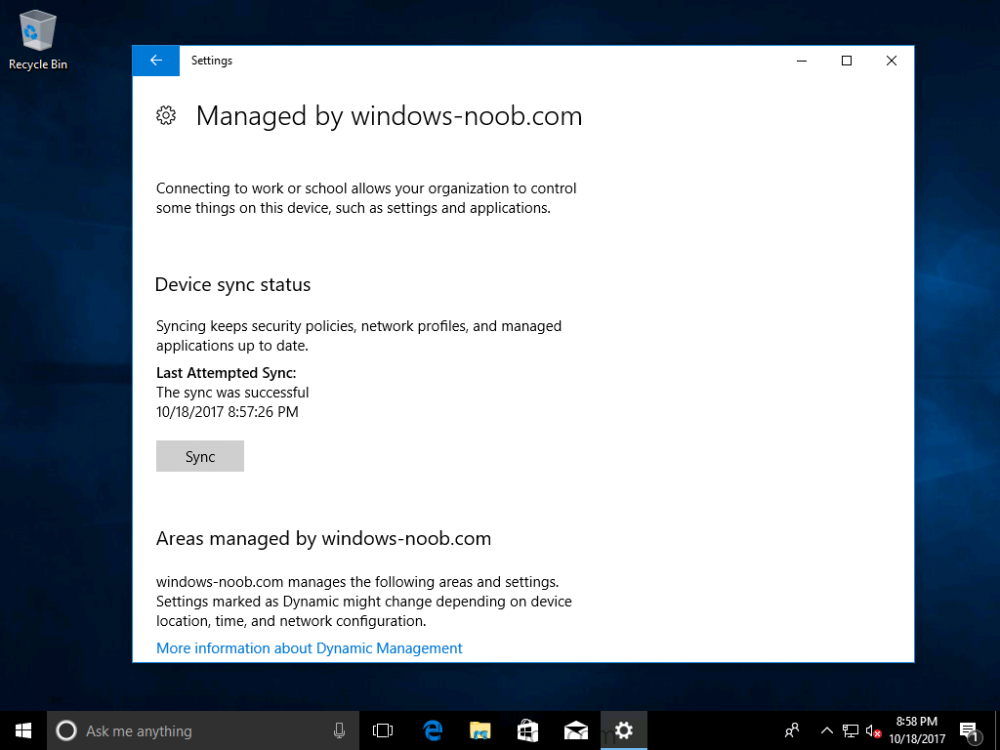
Introduction Devices can be enrolled into Microsoft Intune in many ways, the user can download the Microsoft Company Portal, and enroll the device using the wizard contained within that app, this would then mean the device shows up as Personal owned. Or, the admin can use Bulk Enrollment methods such as Apple Device Enrollment Program or Apple Configurator (which requires an Apple Mac to run the program) or for Windows devices, use Windows AutoPilot. Keep in mind that bulk enrollment is generally for new devices and not devices that have already been deployed. When you join new Windows desktop, mobile, holographic or Surface devices into Azure AD (Azure AD join as part of OOBE or Windows AutoPilot or via the options in the operating system) you can avail of a new MDM auto-enrollment capability which means that not only is the device Azure AD joined, but it will automatically become enrolled (and managed) by Microsoft Intune. This also means that the device will show up as Corporate owned and has the distinct advantage of not needing the end user (or admin) to have to download and use the Company Portal to enroll the device. To setup MDM auto-enrollment in Azure is fairly easy, and here's how to do it. You do need to have both Azure Active Directory Premium subscription and a Microsoft Intune tenant configured before doing this. Step 1. Login to Azure As a user with administrative permissions in Azure Active Directory, login to https://portal.azure.com and select the Azure Active Directory service highlighted here with the red arrow. Step 2. Configure MDM auto-enrollment Click on Mobility (MDM and MAM) and then select Microsoft Intune from the applications listed. The Configure Microsoft Intune blade opens. Notice the following text (by clicking on the information 'i' beside MDM User scope, which explains the capabilities. Use MDM auto-enrollment to manage enterprise data on your employees' Windows devices. MDM auto-enrollment will be configured for AAD joined devices and bring your own device scenarios. Click on Restore default MDM URLs and then select Some (to select one or more user groups you want to enable for MDM auto-enrollment), or All to apply to all users. In this example you will add a User Group (previously created, containing one or more Windows device users), so select Some, and then click on Select Groups to select the User groups you want this MDM auto-enrollment capability to apply to. When you are done with your selection, click on Select. Next click on Save to save your changes. You'll be notified in the top right corner of the success or failure of this action. That's it, job done, now go and Azure AD join a Windows device, using a user that is a member of the group you specified above. After joining Azure AD, it will also become MDM auto-enrolled by Microsoft Intune. You can verify this by going into Microsoft Intune service in Azure, and selecting Devices then All Devices, the device you just joined into Azure AD will now also be MDM Managed by Microsoft Intune (due to MDM auto-enrollment) and listed as a Corporate owned device. And on the device itself you can verify in All Settings, Accounts, Access work or school, and click on the username. For more info about this read https://docs.microsoft.com/en-us/intune/windows-enroll#enable-windows-10-automatic-enrollment
-
Hi I'm experiencing issues with enrolling iOS-devices to Microsoft Intune with SCCM 2012 R2. I've done all the steps necessary to start enrolling described in this guide, but when I open the company portal to start the enrollmentprocess I get the following error: Error: MdmAuthorityNotDefined Now, of course, I've troubleshooted this error for awhile. According to this technet-article the problem is as follows: This message indicates that the mobile device management authority has not been designated in Microsoft Intune. and I've gone over the provided solutions with how to enable iOS-enrollment, with Apple Push Notification service certificate. My certificate is valid, and I've tried renewing it, and deleting it and uploaded a new one, none of which have worked. I've backtracked multiple times, starting the entire process of enabling iOS-support multiple times, to ensure I didnt make a tiny mistake, and I have followed the guide perfectly. My virtual environment consists of one domain controller, and one server running SCCM 2012 R2 and SQL 2012. Both servers are running Windows Server 2012 R2. Im using an iPhone 6+ with iOS 8.3 I have been able to enroll a Samsung Galaxy S5 without any problems, and I've been able to publish apps to it aswell. Have anyone experienced anything like this? If there is any other information that would help resolving this issues then please ask, and I will try to provide it.