Welcome to windows-noob.com!
Logging in will allow you to download scripts used in the guides.
If you came here looking for the Endpoint Manager step-by-step guides then please start here.
Register for free and ask your questions in our forums.
- 1 reply
- 5283 views
- Add Reply
- 15 replies
- 19584 views
- Add Reply
- 8 replies
- 11851 views
- Add Reply
- 0 replies
- 5876 views
- Add Reply
- 0 replies
- 5307 views
- Add Reply
- 1 reply
- 6373 views
- Add Reply
- 5 replies
- 9268 views
- Add Reply
- 1 reply
- 4794 views
- Add Reply
How to create a collection of systems which do not have a file in a specific folder?
By Codename_Falcon,
Can anyone help me with building a collection of systems which are missing a file in a specific folder?
I have already enabled software inventory for that file type.
Thanks!
Building a Windows 11 24H2 Reference Image using SCCM in Workgroup
By keywan,
Hi,
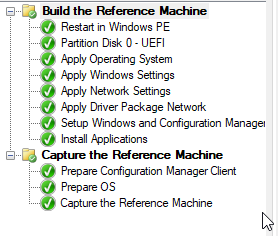
I am trying to build and capture Windows 11 24H2 Reference Image using SCCM in Workgroup. As I know sure, you cannot Build and Capture if the machine joined the domain.
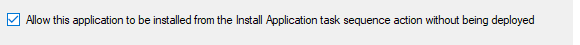
The TS does works and Build and Capture the Image of Windows 11 24H2, but it cannot install any Application.
I put on the Step "Setup Windows and Configuration Manager"----> Installation Properties: DNSSUFFIX=adamix.com SMSMP=cm03.adamix.com
and try with that option too
DNSSUFFIX=adamix.com SMSMP=C
SSRS SCCM Reporting Log
By Cerberus24,
Hi Anyweb,
I’ve started noticing an issue with our SSRS reporting portal. When attempting to run certain reports, I receive the following error:
At the same time, I’m seeing the following entries in the sccmreporting.log on our SQL server (which also runs SSRS):
08/05/2025 17:11 EnableRbacReporting key exists. Value = 1
08/05/2025 17:11 A specified logon session does not exist. It may already have been terminated.
The timestamps in the logs appear to align with the error, a
New Boot Image from USB Stick WinPE keeps restarting
By rolson,
Hi everyone,
We are running Microsoft Configuration Manager Version 2403, Site Version 5.0.9128.1000. We always had a working boot image x64 with OS Version 10.0.19041.1. Our ADK Version is 10.0.22621.1.
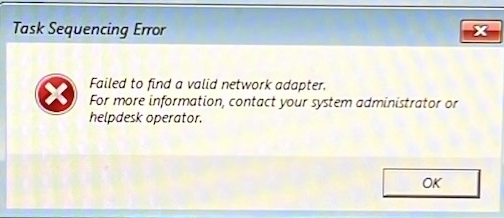
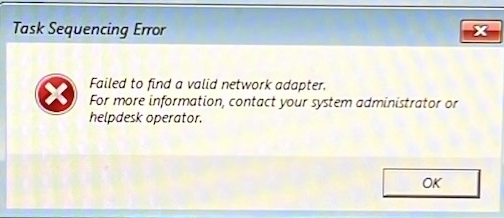
This boot image works on all our devices. Recently we received new hardware and with our working "old" bootstick we receive the error message "failed to find a valid network adapter". In smsts.og:
"GetAdaptersInfo() failed."
VerifyNetworkAdapter() failed. 0x800700E8"
Sin
Build and Capture a referenz OS Image Windows 11 build 24H2 issue
By keywan,
Hi,
I have created a new TS for Build and capture Windows 11 Build 24 H2 using Workgroup and NOT DOMAIN.
I am using SCCM2403
It is working and it is creating a WIM File, but my selected Application did not install
my setting on the following Options
Configure the network
Join a workgroup
Workgroup: DOM
Install the Configuration Manager client
Select the Configuration Manager Client Package package
OSD Task Sequences failing on Install Software RPC error
By jbudd0649,
We are a small school district in northern VA, every summer we wipe and reload all of our Windows PC's so that the students and staff have a fresh PC at the beginning of the year. Each school has a task sequence unique to their building for software programs. All software is being deployed via the package model during the TS. I recently upgraded our server to CM 2503. We do not use intune nor do we have any type of cloud presence. We have been imaging PC's this way for years. This issue just sta
Can I upgrade my SCCM Server from 2403 directly to 2503 or should I upgrade first to 2409?
By keywan,


Hi,
At the time I have running SCCM 2403 with hotfix. Can I upgrade it directly to the new Version 2503 without any issue? Or should I first upgrade to 2409 with hotfix and then to 2503?
Thank you for help.
Regards
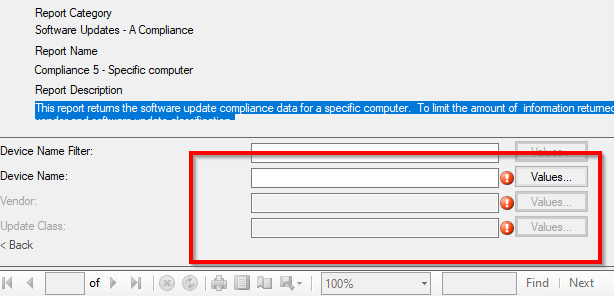
Create a Report by SCCM 2403 issue with Value
By keywan,
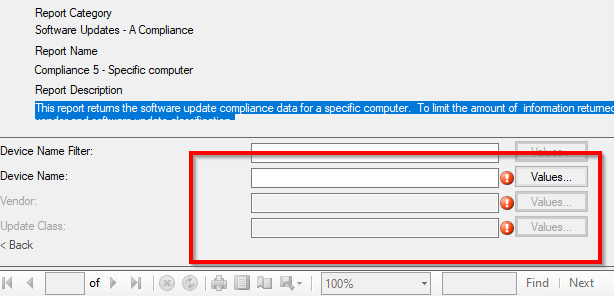
Hi,
I am trying to create on the SCCM 2403 an Report for example for "Complaince 5 - Specific computer. As you know, it should fill many "Valuses" to create an Report.
IS there any way select all Values together as "ALL"?

