teamfox201
Established Members-
Posts
90 -
Joined
-
Last visited
-
Days Won
1
teamfox201 last won the day on February 10 2014
teamfox201 had the most liked content!
About teamfox201
- Birthday 08/04/1984
Profile Information
-
Gender
Male
-
Location
CA
Recent Profile Visitors
3568 profile views
teamfox201's Achievements
-
teamfox201 started following Branch sites with slow WAN , SCCM 1810 Application Approval Request Emails , Evergreen and 7 others
-
Evergreen
teamfox201 replied to rob343's topic in System Center Configuration Manager (Current Branch)
https://cloudhouse.com/resources/evergreen-it https://www.computerweekly.com/feature/The-importance-of-adopting-an-evergreen-IT-strategy -
MBAM BitLocker - Mainstream support ends July 2019
teamfox201 replied to Hedbye's question in Windows 10
Started BitLocker POC about a month ago. Initially had MBAM in the design but after learning it was going away I decided to stick with keys in AD. We are not currently using Azure or Intune. -
I have been looking at the Config Manager Antivirus Exclusion list (https://blogs.technet.microsoft.com/systemcenterpfe/2017/05/24/configuration-manager-current-branch-antivirus-update/) and was wondering how others have this organized. I am looking at having at least 2 policies (Workstation and Servers) but for servers, are you adding all the exclusions under one policy or making it neater in the console and making a new exclusion policy for SQL, IIS, ConfigMgr, etc.?
-
Meltdown/Spectre Application
teamfox201 replied to JBC's topic in System Center Configuration Manager (Current Branch)
Good find!! Your question sparked curiosity about our environment but we still have Powershell 2.0 on Windows 7 systems. -
I think i found my answer, it is a "feature" in 1802 that will get expanded on in other updates... https://configurationmanager.uservoice.com/forums/300492-ideas/suggestions/8782225-enable-a-column-for-primary-user This is fixed in the just shipped #SCCM 1802 release. For both Primary User, and Logged on user. We still will improve a couple things:1) it is only in devices views; and we will add it in more views (collections, etc.)
-
Meltdown/Spectre Application
teamfox201 replied to JBC's topic in System Center Configuration Manager (Current Branch)
To be fair, I have not tested this method but I do not see a reason it would not work as long as the return codes are properly returned and captured during deployment. I would use the application developed by Steve Gibson https://www.grc.com/inspectre.htm . Don't let the basic website fool you, he is reputable. Package that up in SCCM with the "probe" command , and based on the exit code returned to SCCM you should get a pretty good picture of which systems are vulnerable. I just noticed in release #4 , he gives you sample scripts you can use: https://www.grc.com/inspectre/InSpectre-Probe-Samples.zip Release #4 — Silent System Probe Option:When InSpectre is launched with the string “probe” in its command line, its Windows user interface will be suppressed and InSpectre will act like a command-line utility. It will assess its hosting system's status, then immediately terminate itself returning a decimal exitcode which encodes the eight “trouble bits” shown below, which itemizes any trouble. Therefore, for example, an exitcode of zero (0) is returned only by a fully secure system. Decimal Value Trouble Itemization 1 OS is not aware of the Meltdown vulnerability 2 OS is not aware of the Spectre vulnerability 4 The system is vulnerable to Meltdown 8 The system is vulnerable to Spectre 16 CPU does not support Spectre (microcode not updated) 32 CPU does not support low-overhead Meltdown protection 64 Meltdown protection disabled by registry setting 128 Spectre protection disabled by registry setting -
Not sure if this is a bug in SCCM 1802 or if it is a new "feature" but I am seeing it in the production environment and also my lab. Anyone else notice this and any idea what may be going on? When looking at the "Devices" collection, all the columns for Primary User(s) , Last Logged on User, and Last Logon Timestamp show data correctly. When I create a new collection, for example a Windows 10 Workstations and add Primary User(s) , Last Logged on User, and Last Logon Timestamp... all the columns are blank, even if "Devices" collection has data in them.
-
Are these buttons useless while using Sccm now. Check for updates is not entirely useless with SCCM, it forces Windows to check your local WSUS server for updates. How can i confirm my devices are actually pulling End point updates from SCCM. Definitely get familiar with the SCCM Client log files: https://docs.microsoft.com/en-us/sccm/core/plan-design/hierarchy/log-files#BKMK_ClientLogs You can look through these log files: C:\Windows\CCM\Logs\DataTransferService.log - see where its pulling the AM_Delta_Patch_x.xxx.xxx.x.exe from. C:\Windows\WindowsUpdate.log - Follow what the log says on Windows 10 to actually get the log content. C:\Windows\Temp\MpCmdRun.log Is it necessary for me to allow the "Check online for updates from Microsoft update." link to remain active No it is not necessary and you can turn it off with GPO (see Do not connect to any Windows Update Internet locations in the link below) https://docs.microsoft.com/en-us/windows/deployment/update/waas-wu-settings
-
If you have verified the systems are no longer around and do not need the client installed, I would right click the computer name and look at properties. Then look at the value for agent name. If it says AD System Discovery (and those systems are no longer around) then delete the record from Active Directory. If the agent name says something else then figure out how to clean up that discovery method so obsolete systems do not get pulled back in during every sync. https://docs.microsoft.com/en-us/sccm/core/servers/deploy/configure/about-discovery-methods
-
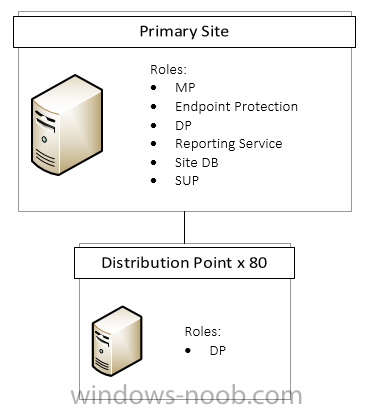
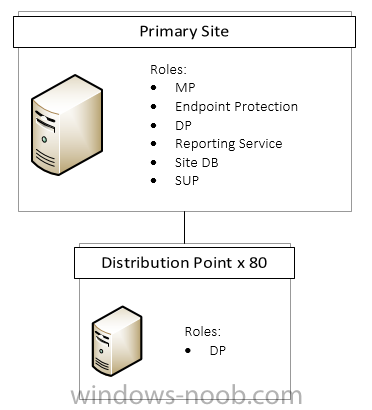
Hello, Looking for some assistance on getting large packages (task sequence, windows updates, etc) to distribution points with slow WAN speed. We have about 80 sites averaging 1.5 - 3 mbps back to HQ and we cannot impact their network during the day with SCCM distributions. Currently have the rate limit on those DP's configured to 50% during business hours. With driver updates and Microsoft Monthly Rollup patch bundles growing large in size, it takes forever to get the packages to all the distribution points even over the weekend. For example: Windows 10 patches for 2017 is reporting to be 3.5 GB and that's just one package. Looking for tips and tricks from what others are doing to overcome these bandwidth limitations without impacting their slow sites.
- 2 replies
-
- bandwidth
- network speed
-
(and 1 more)
Tagged with:
-
Hello, I am sorry for the double post (SCCM 1610 Cloud Proxy Service), I couldn't figure out how to edit/delete the title but i wanted to have the correct words in my post. I am looking for some clarification on setting up the Cloud Management Gateway in SCCM. We have a primary site (managing about 6000 clients) and about 80 distribution points at small offices with 3mbps or less WAN speed. We are looking into managing remote machines that are not in the office and the Cloud Management Gateway looks pretty promising. The question I have is, do we need to set up another primary or just another DP (like the small office config) but with the MP, DP and SUP roles using HTTPS? Trying to avoid having to set up another primary and then adding a CAS if possible.
-
Hello, I am looking for some clarification on setting up the Cloud Management Gateway in SCCM. We have a primary site (managing about 6000 clients) and about 80 distribution points at small offices with 3mbps or less WAN speed. We are looking into managing remote machines that are not in the office and the Cloud Management Gateway looks pretty promising. The question I have is, do we need to set up another primary or just another DP (like the small office config) but with the MP, DP and SUP roles using HTTPS? Trying to avoid having to set up another primary and then adding a CAS if possible.