Search the Community
Showing results for tags 'endpoint protection'.
-
We are getting ready to get rid of our AV solution and are looking to use SCCM Endpoint Protection instead. Is this enough? Are we still going to be protected as we were with a full blown AV? We are fully Windows 10 going forward. Is there a document that will walk me through setting this all up? Is there a way to setup email alerts when a virus / malware / other security alert is found? Anything else we need to know before starting?
-
Currently running CM1806 and looking into Endpoint Protection as a replacement for our current AV. I have the role installed and tested it to 1 pc and it all seems great, but I don't know where to go from here? Is there some kind of setup guide I can follow with best practices included? I have a lot of questions before I even begin really testing this? What OS's is this compatible with? Will it work on Server OS's (2008, 2012, 2016)? Just looking for some guidance on what my next steps should be.
-
Hi, I've recently had an issue were my Windows 10 1803 clients don't get signature updates although the definition updates seem to apply ok. Looking through the logs nothing really stuck out except that the machine didn't have a antimalware policy. I check SCCM and the policy is deployed and apperently installed ok (going from the console). Any ideas would really be great!
-
- sccm
- endpoint protection
-
(and 1 more)
Tagged with:
-
Hi, We have recently noticed that the client has stopped automatically installing onto laptop/desktops. We have had everything run successfully for over 6 months and I have spoken with other administrators and nothing appears to have changed on the domain. Once imaged you can see within C:\Windows that the 'ccmsetup' folder has been copied across but not further action has taken place. In order for the client to install correctly with Endpoint Protection I have to manually run the client.exe file. After this process Endpoint Protection is installed and I can see SCCM now states the machine has the client installed, allowing for remote control, deploying software etc etc. Post image I have noticed on Configuration Manager that the Client Certificate states 'None' rather than 'PKI'. Has anyone else experienced this problem and/or recommend the appropriate logs to be reviewing. Thanks
-
In our environment (Windows 7 32 bit) we use System Center Endpoint Protection. The client is working and gets settings from System Center 2012 R2. Scans are working, updates are working etc. The updates come from the System Center Server. There is an option in Endpoint Protection to manually update the virus and spyware definitions, but when we try this option we get an error (0x8024002e) Unfortunately the message is in dutch, but 'Bijwerken' means 'Updating' and as you can see it doesn't work. We've tracked the issue to Windows Update being disabled on the client. We don't want the clients to have the option to get updates from the Microsoft Update website. With Windows Update enabled clients can bypass our policies and download updates that are not approved by us, for instance Internet Explorer 11. That is why updates are managed through System Center and all access to Windows Update is disabled. Does anyone have the same issue? Can someone explain if it is normal for System Center that clients can bypass the settings we defined for updates? I expected that once we enabled software updates on clients through SCCM that users would not be able to bypass those settings by going to the Microsoft Update website to look for updates. Did we do something wrong in the configuration? Does SCCM need extra policy settings to manage updates? These are our update settings. As I said before... Endpoint Protection receives it's definitions, so that is OK, but there is a rather annoying error when trying to manually update the definitions. Any help is appreciated since Google gives no clues for this error other than enabling Windows Update. That would be ok if we could deny users access to the Windows Update site, but we have not found that option yet.
- 1 reply
-
- system center
- endpoint protection
-
(and 1 more)
Tagged with:
-
Hello, I currently have Microsoft endpoint protection on computers across a campus. I would like to deploy SCEP across my campus so that we can monitor and maintain it all from the server. This will require deploying the SCEP client over the network. My problem is: It creates pop ups for the current user logged in saying that windows defender is out dated and scep is out dated. Is there any way to install SCEP silently without the user being notified? I can deploy SCEP updates almost immediately afterwards to get rid of the "at risk" notification in the task bar, but it still gives users security warning popups, which i cannot have when i deploy all across campus.Thanks
-
EP 4.2.223.1 is installed, version is higher than expected installer version 4.1.522.0 Has anyone see that in the EndpointProtectionAgent.log on a system they have been trying to push the SCCM client to before? We have a number of servers that haven't reported back to SCCM that their Endpoint Protection is being managed. Looking at the log noted above has that error. A snipped from the log: A few of these systems were previously manged under a dev SCCM 2012 SP1 install, and some under FEP 2010. Now we are deploying from a new SCCM site that we have setup to these servers. Does this indicate that we need to update the EP install that we are pushing out?
-
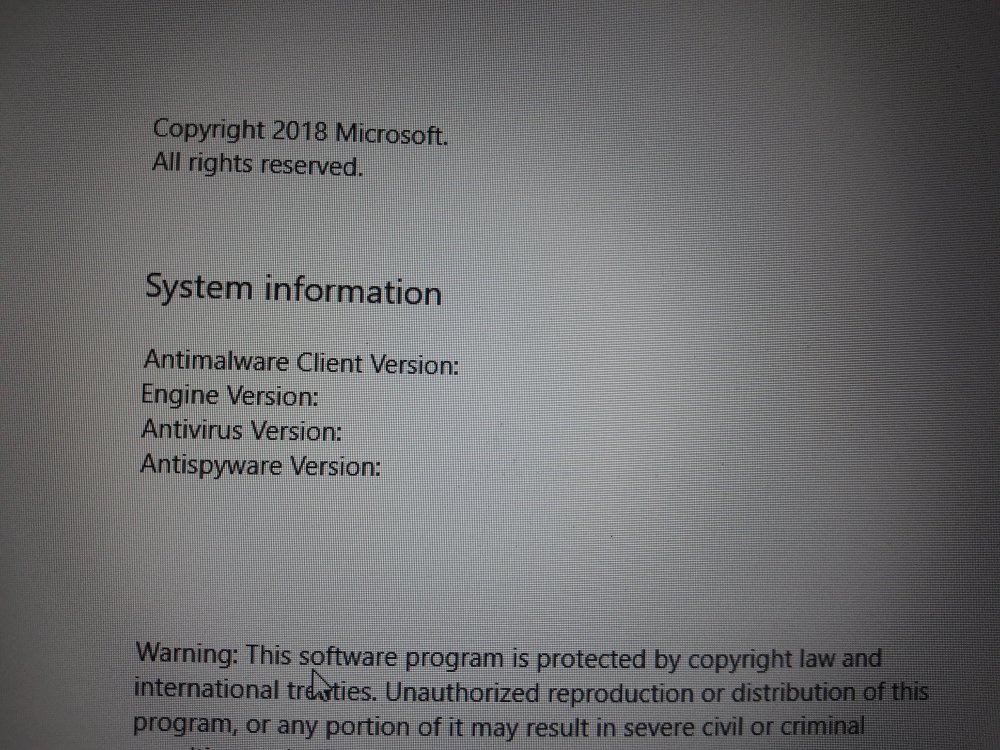
Hi Guys, I'm experiencing some pretty funky anomalies with System Center Endpoint Protection 2012 and wondered if anyone could point me in the right direction. We are running CM12 RTM on Windows 2008 R2 SP1. My SUP, Antimalware definition updates, Policy application, client deployment (etc) have worked autonomously and reliably for quite a while now. Over the past day or so, the propagation of updates to my clients has ceased and EVERY instance of the client has the same anomaly. When I open the 'About SCEP' element of the client that displays the engines, product versions, NIS versions and so on, instead of seeing it fully populated with that information all I see is... System Center Endpoint Protection Version: 2.2.903.0 Antimalware Client Version: 3.0.8410.0 These are clients that have worked flawlessly and also those currently being installed as a part of OSD. It's important to note that this has only occurred since the CAS and PRIMARY site servers were rebooted a day or so ago. The SUP synchronization works fine, there are no component errors and the ADR is running and downloading a package that's set to deploy and is distributed to all DPs accordingly. Does anyone have any ideas? Ian.