-
Posts
9268 -
Joined
-
Last visited
-
Days Won
371
Everything posted by anyweb
-

How do I add a PowerShell entry in Task Sequence?
anyweb replied to afaik's topic in Configuration Manager 2012
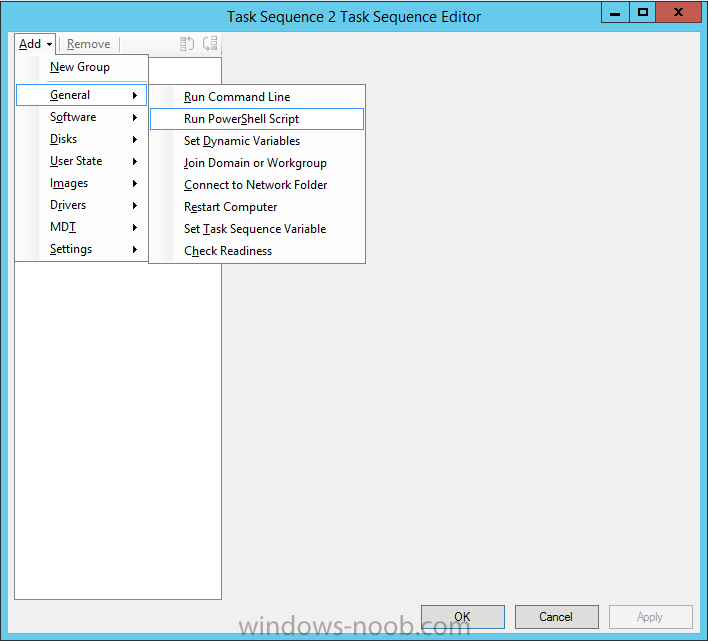
can you show me a screenshot of your configmgr version (about, version) the Run PowerShell script step comes with ConfigMgr R2, so you should have it, however, did you update your console after upgrading ? -

How do I add a PowerShell entry in Task Sequence?
anyweb replied to afaik's topic in Configuration Manager 2012
-

How do I add a PowerShell entry in Task Sequence?
anyweb replied to afaik's topic in Configuration Manager 2012
what version of SCCM are you using ? -
what error do you get, can you attach the smsts.log
-

SCCM 1601- Build a Windows 1o Enterprise
anyweb replied to Sokoban's question in Deploying Windows 10, Windows 8.1, Windows 7 and more...
there's your problem Warning: Matching Processor Architecture Boot Image (0) not found SMSPXE 2016-05-27 14:25:49 4456 (0x1168) make sure to distribute (and enable for pxe) both architecture boot wim's -

SCCM 1601- Build a Windows 1o Enterprise
anyweb replied to Sokoban's question in Deploying Windows 10, Windows 8.1, Windows 7 and more...
what's in between the distribution point and this vm ? is the boot image deployed to the pxe enabled distribution point ? what does the smspxe.log file reveal ? -
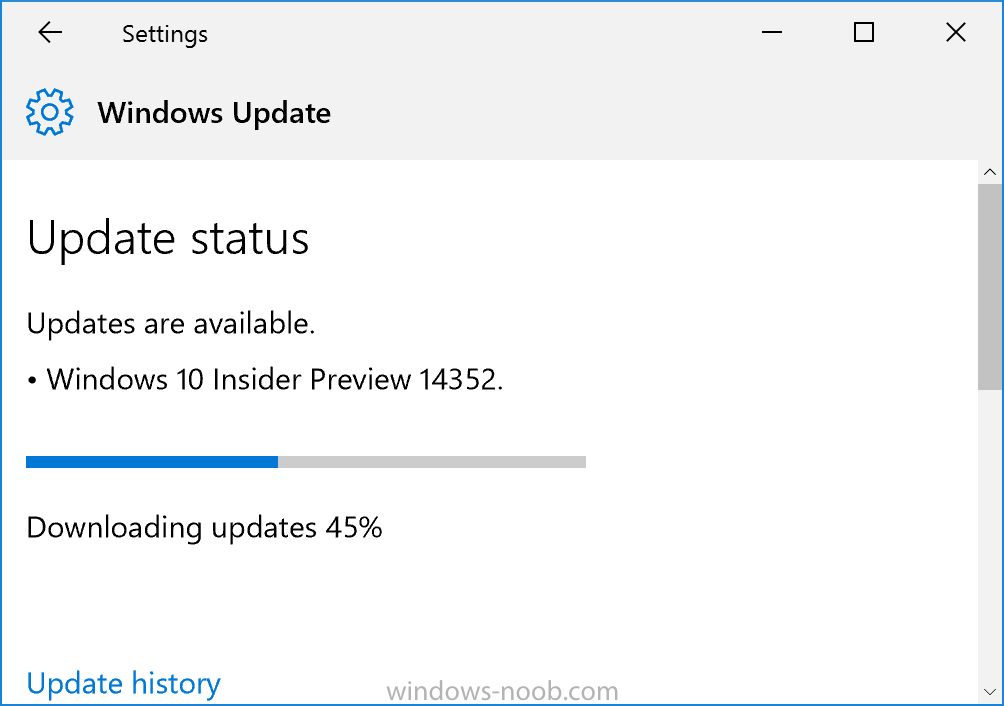
Microsoft has released yet another Windows Insider Preview release, this time it's 14352 more info > https://blogs.windows.com/windowsexperience/2016/05/26/announcing-windows-10-insider-preview-build-14352/
-

Help me understand the workstation pxe boot/boot.wim process
anyweb replied to 92 5 oh's topic in Configuration Manager 2012
that's a long post but to simplify things, you probably just need to add drivers for the network card for the hardware you are PXE booting, to the boot image you use in your task sequence, once you've done that, and then re-distrbuted the boot image to all distribution points, try pxe booting again, does it work, or fail ? -
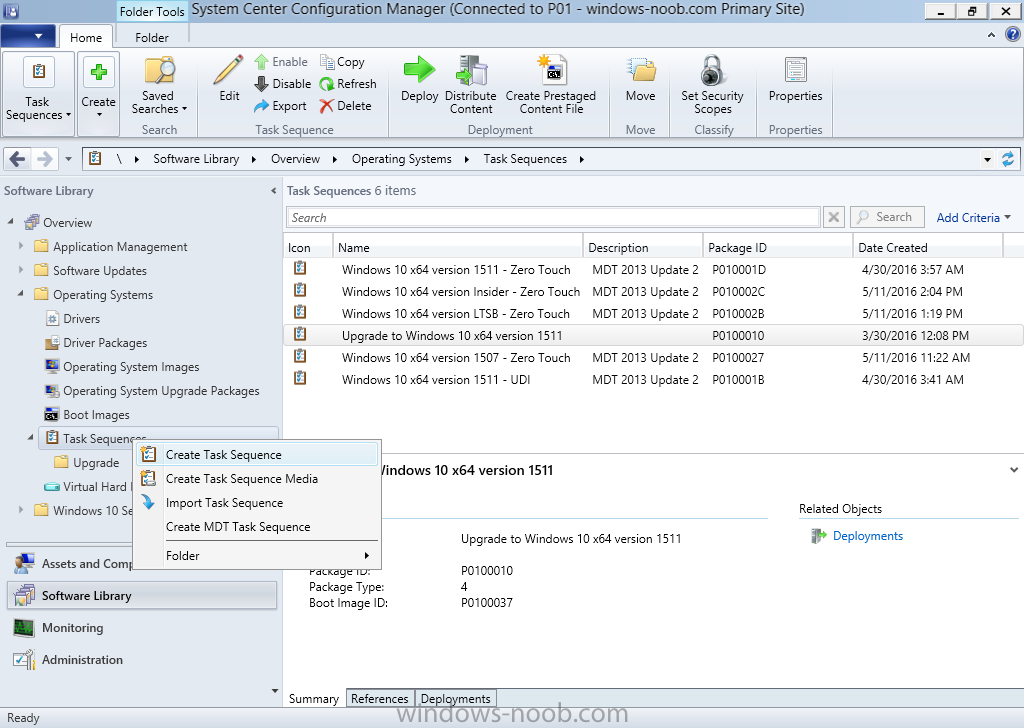
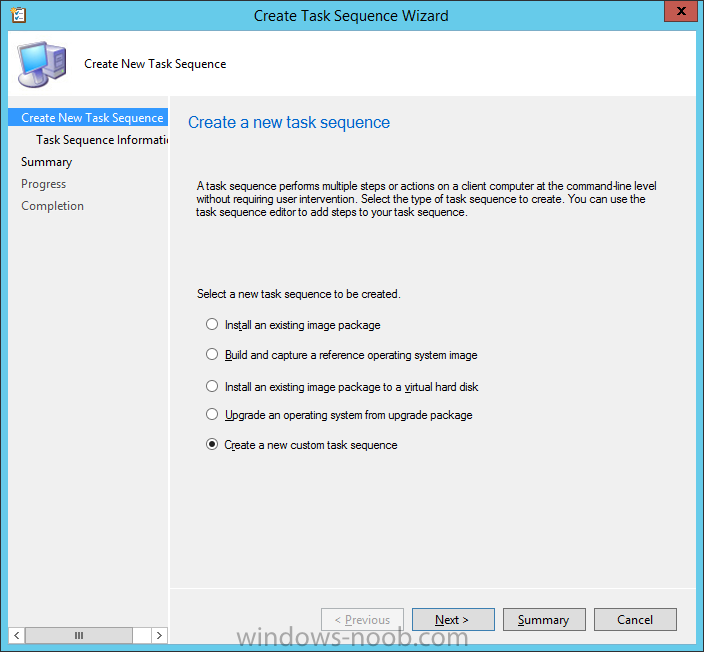
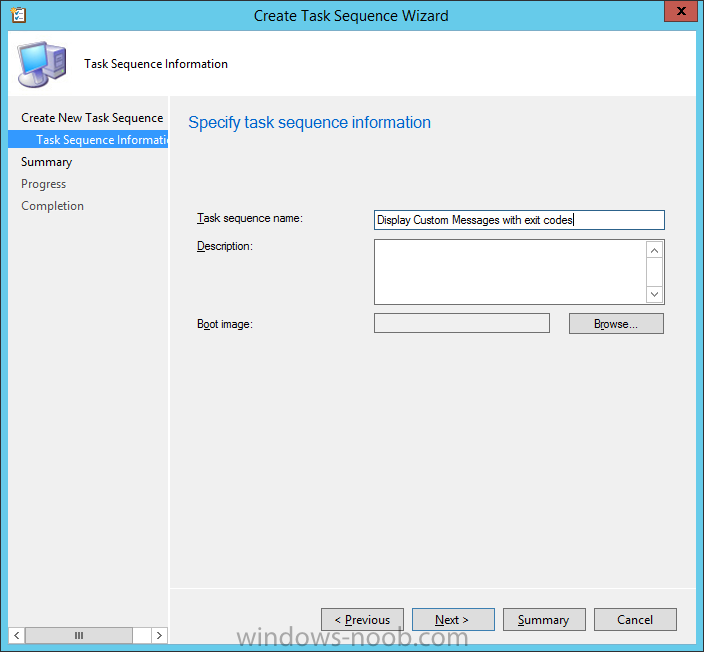
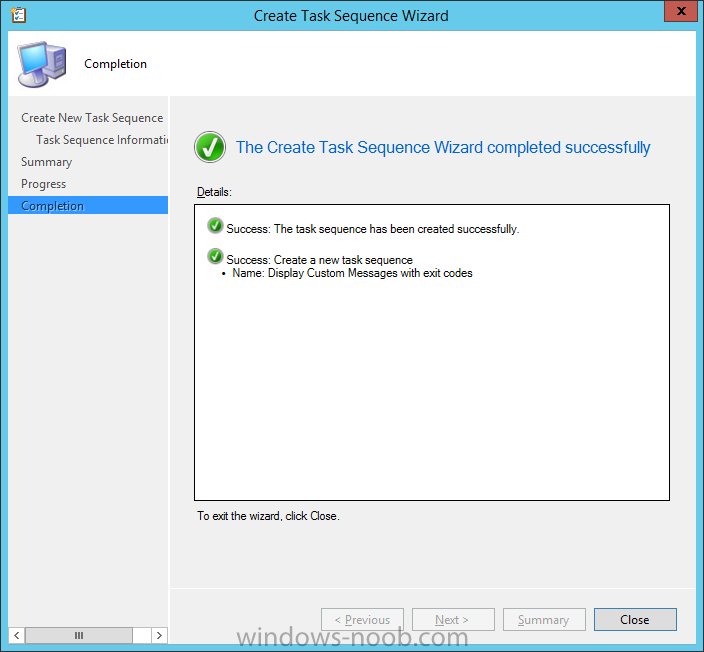
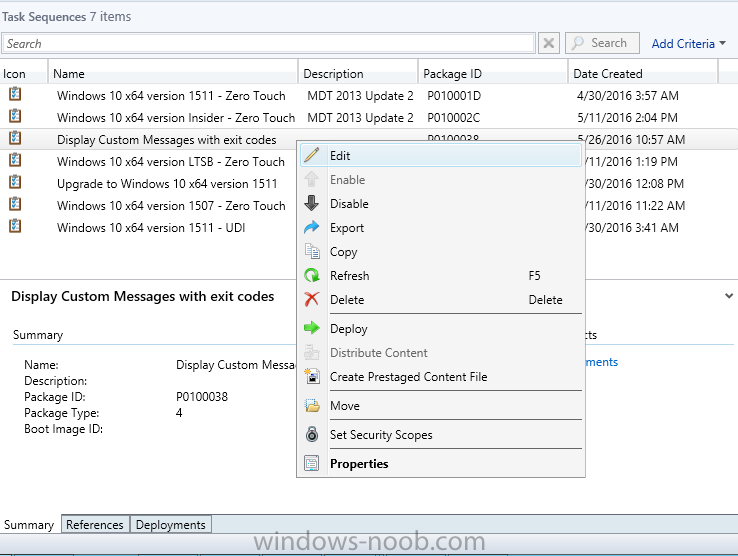
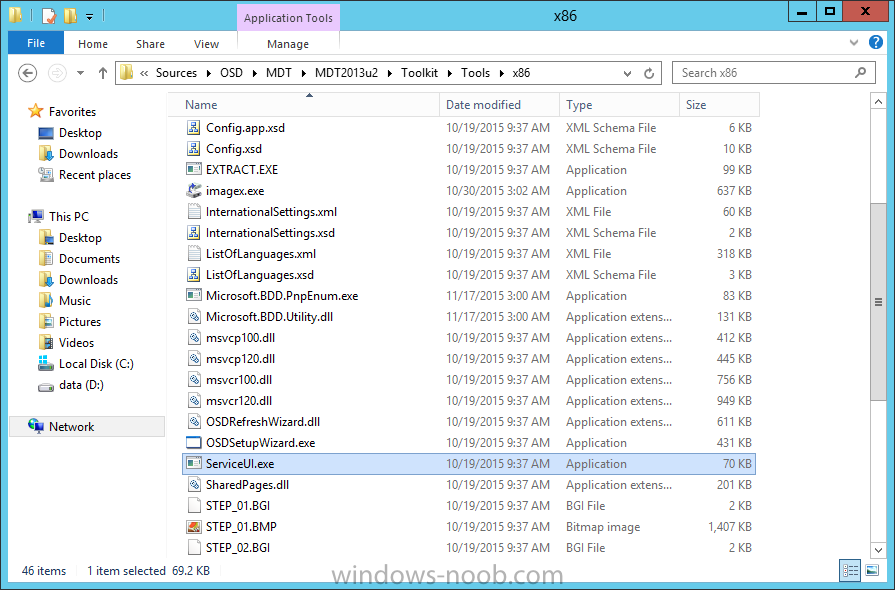
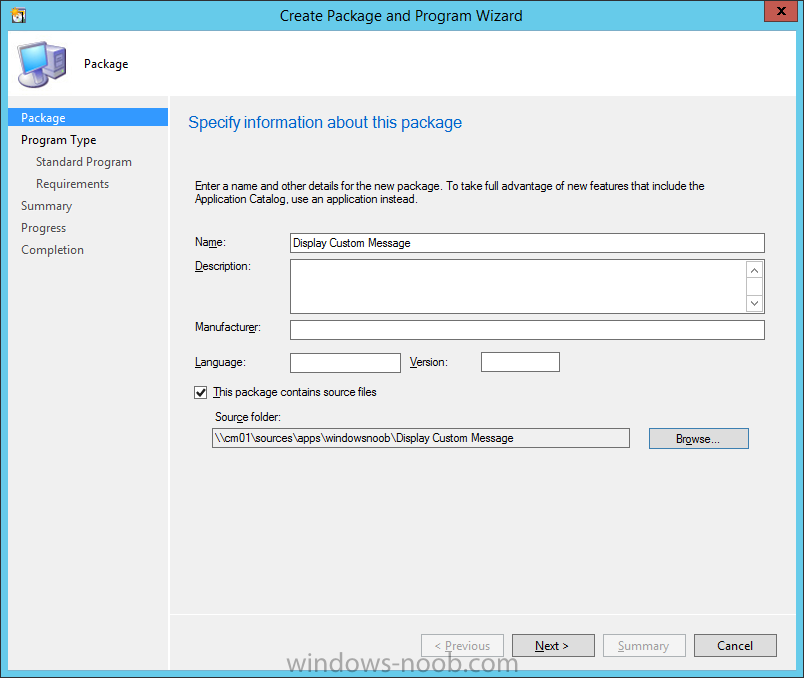
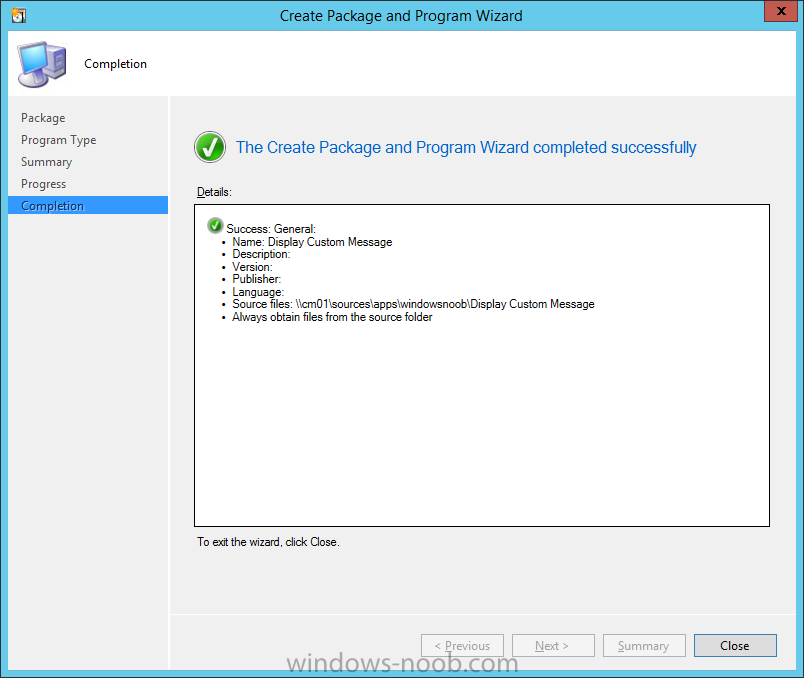
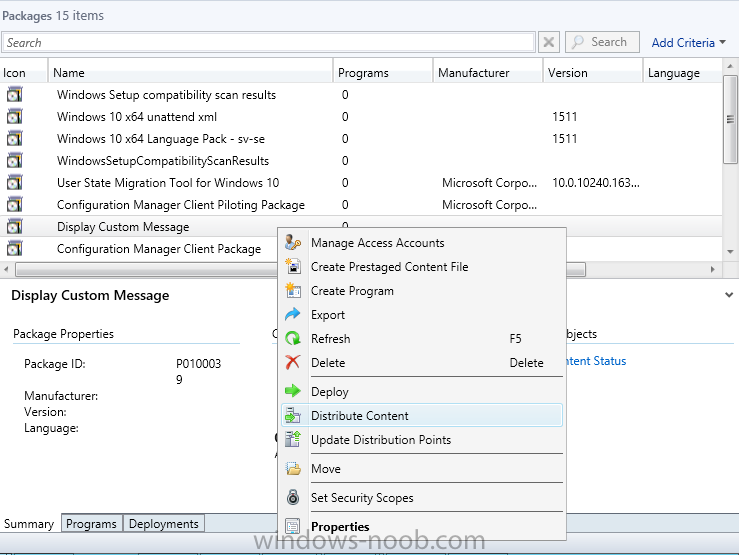
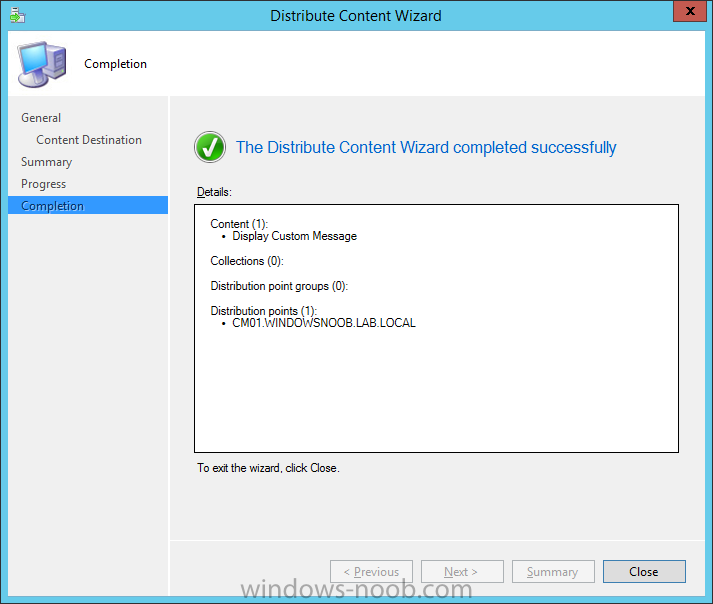
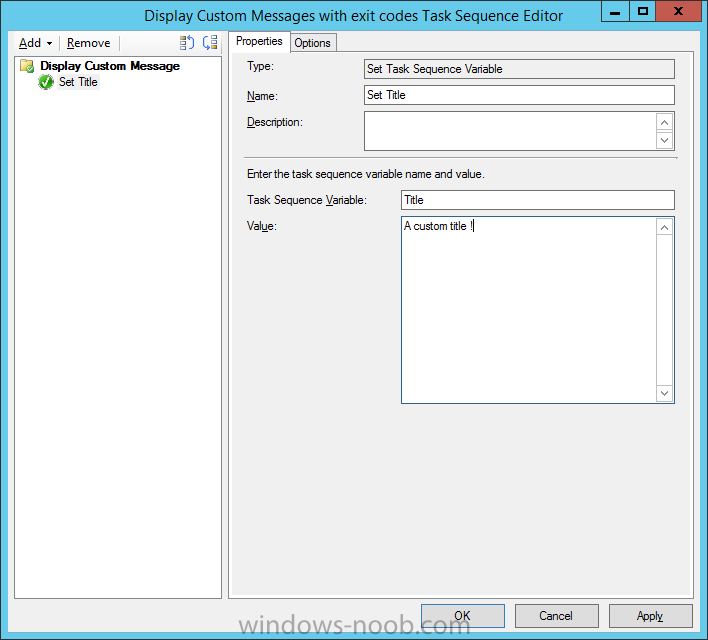
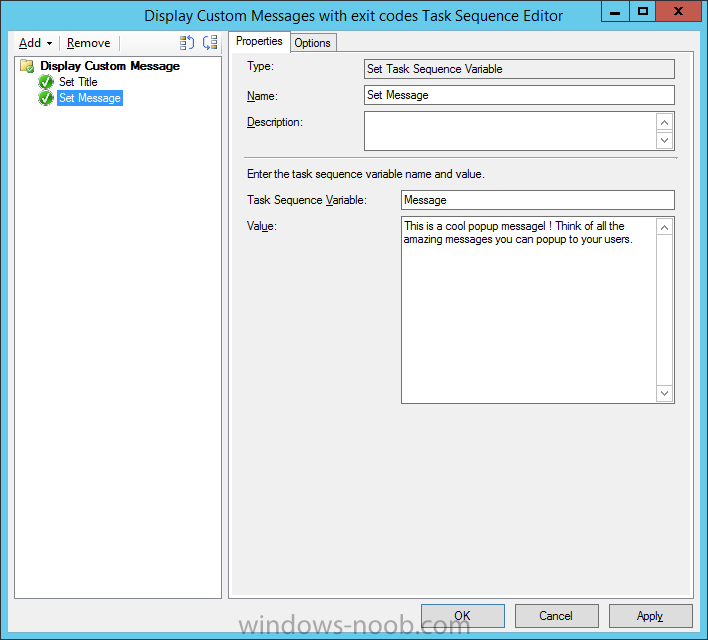
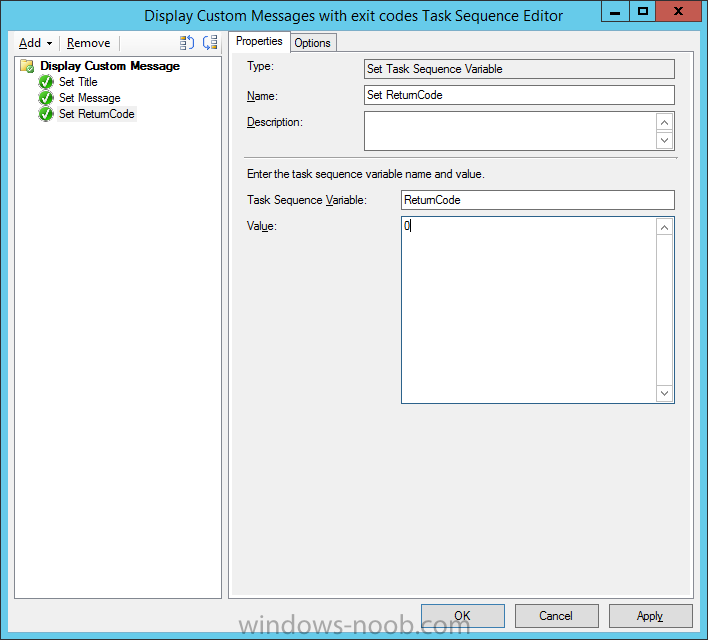
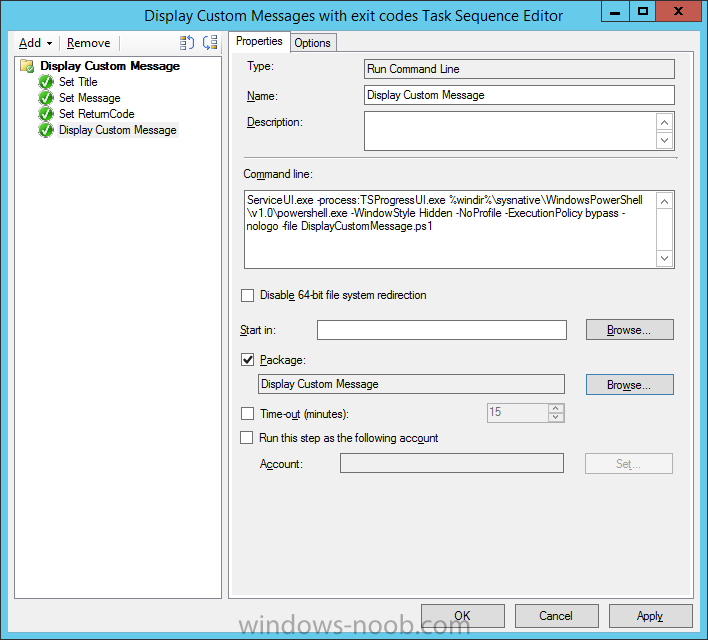
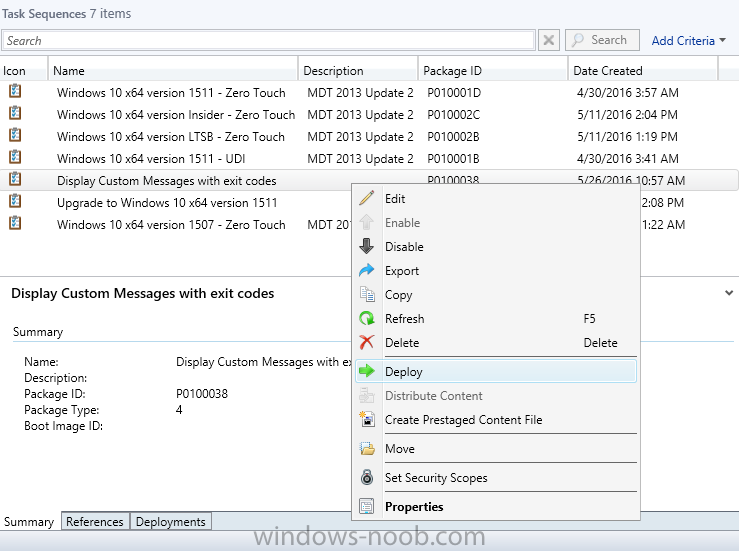
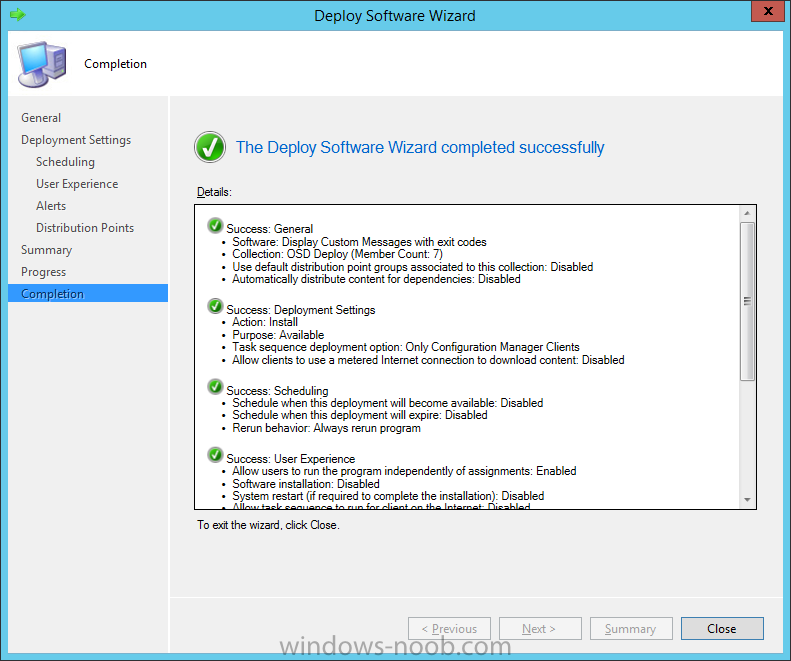
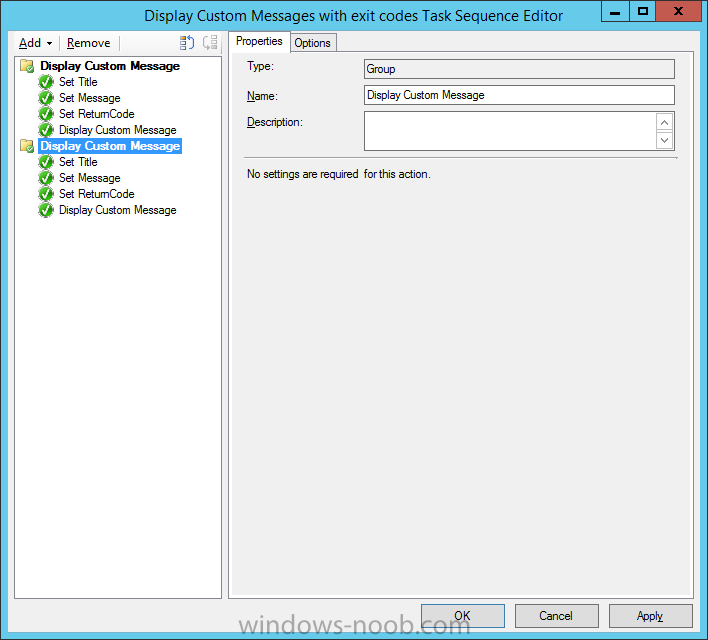
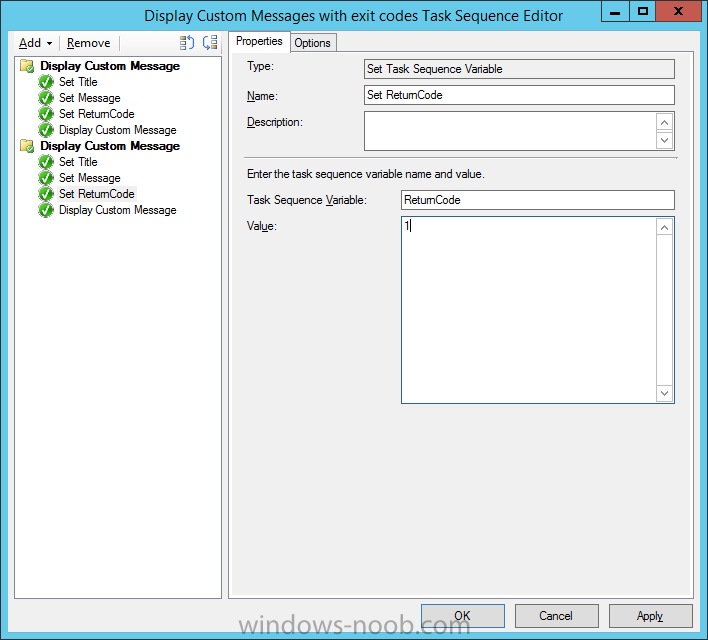
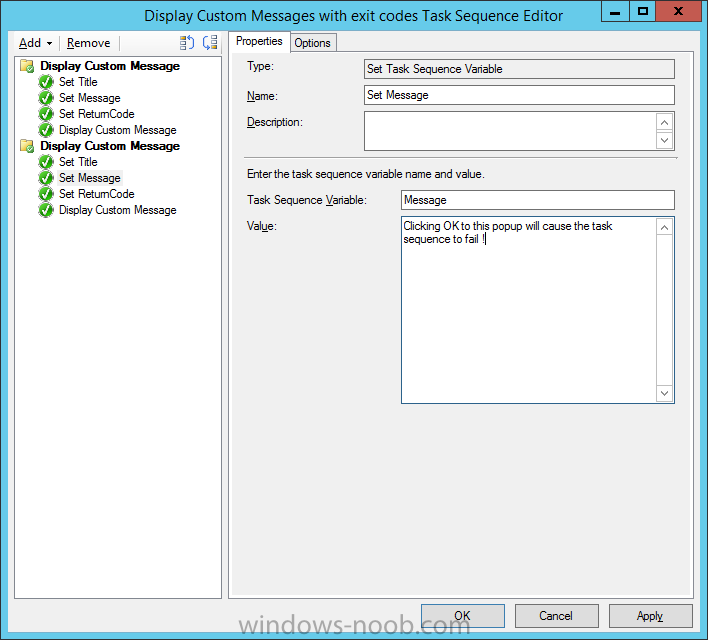
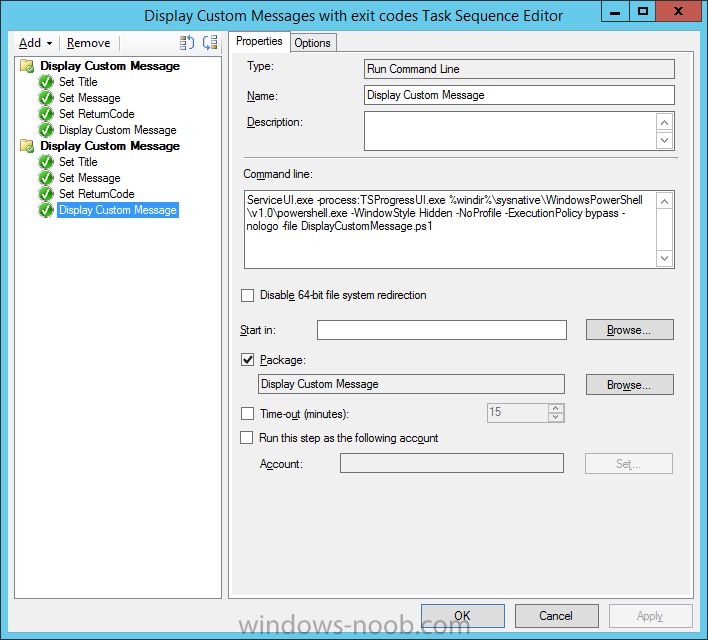
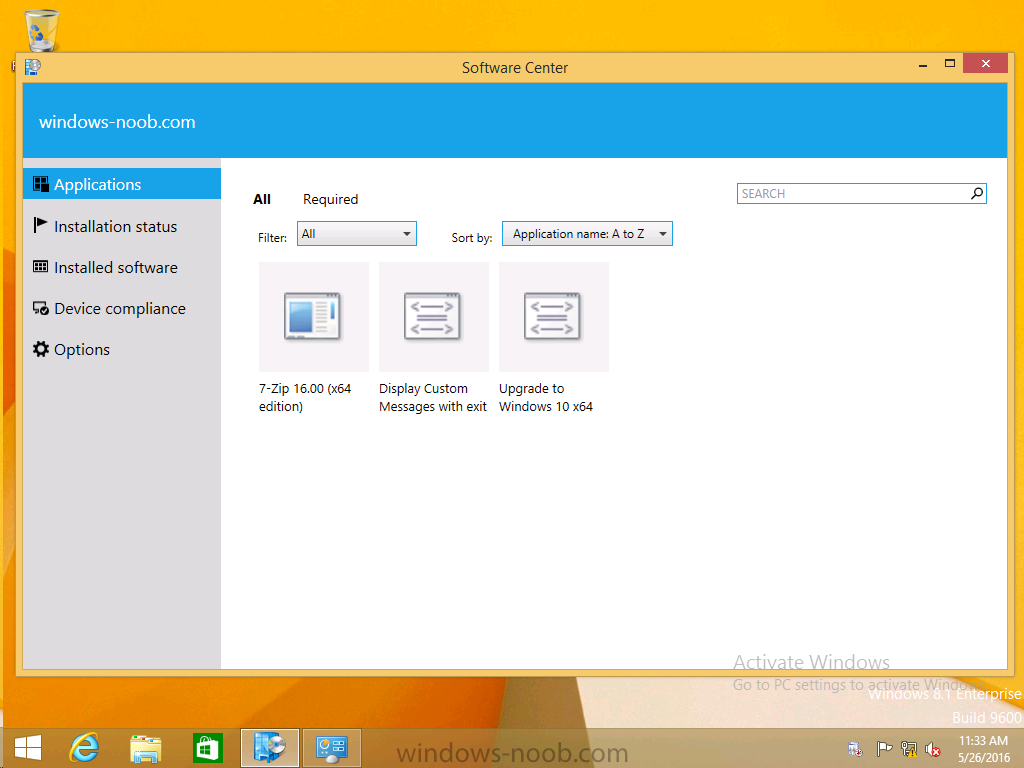
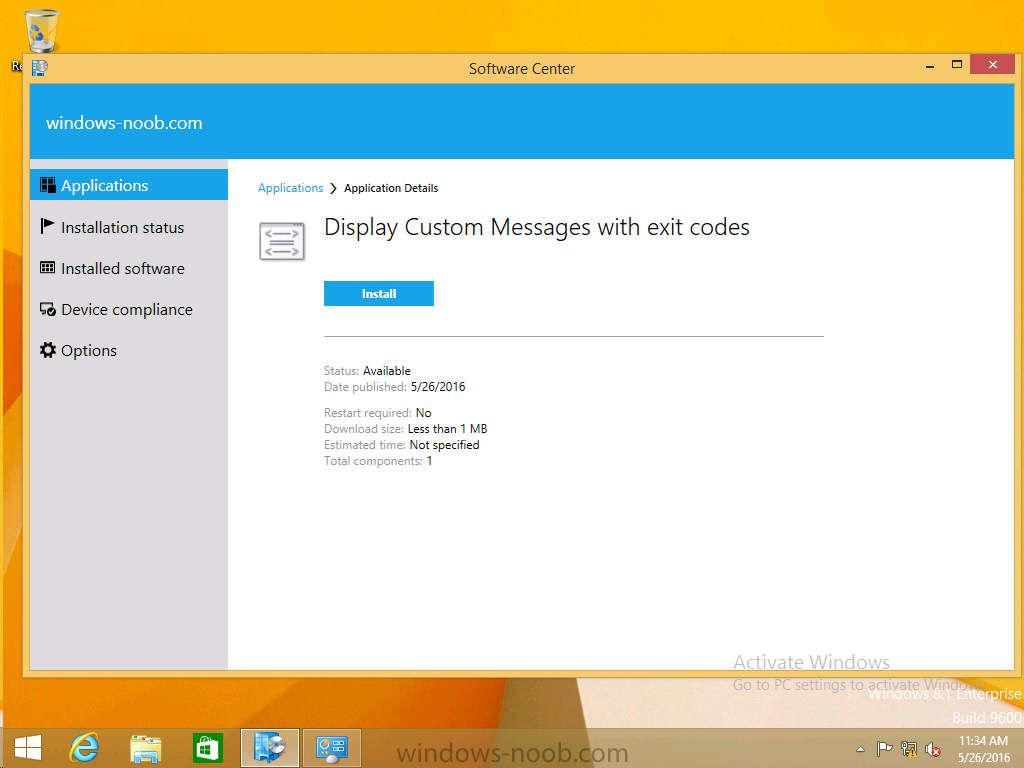
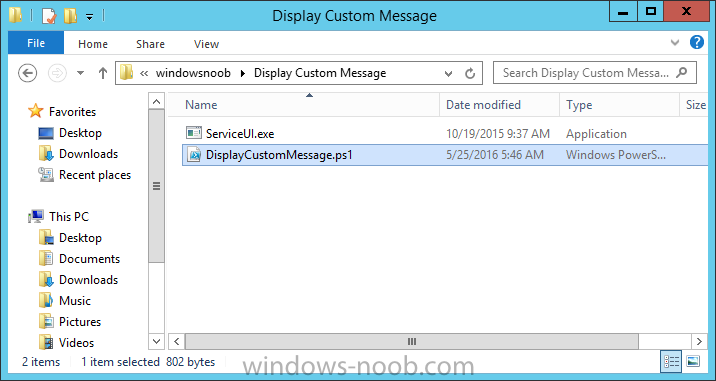
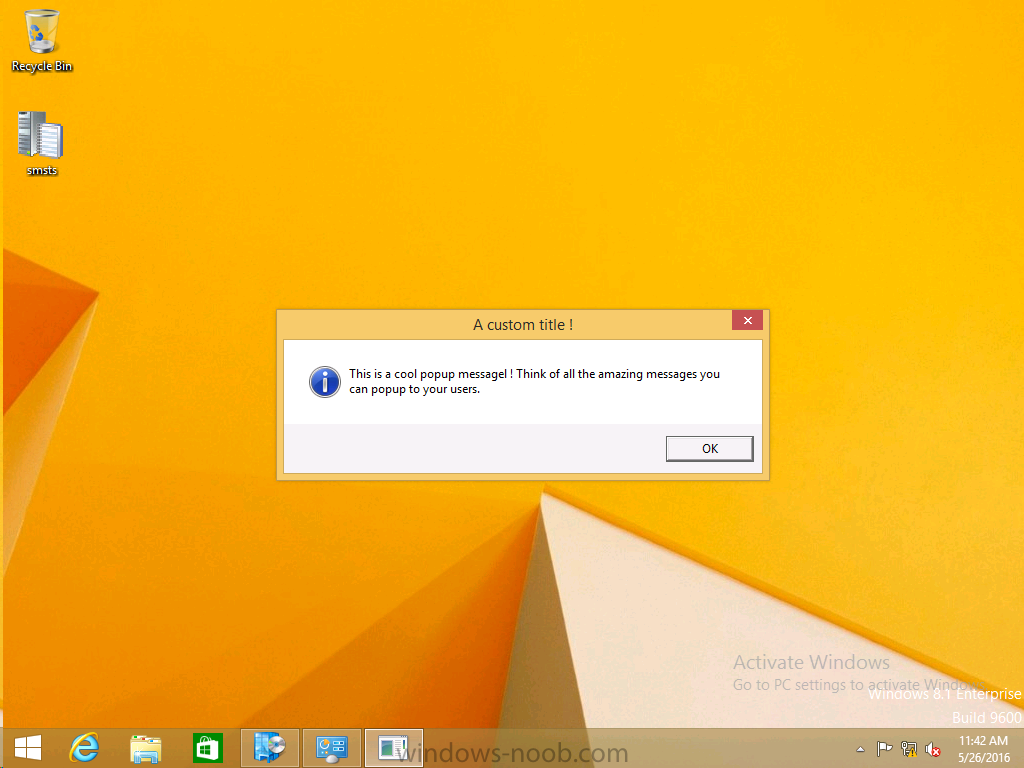
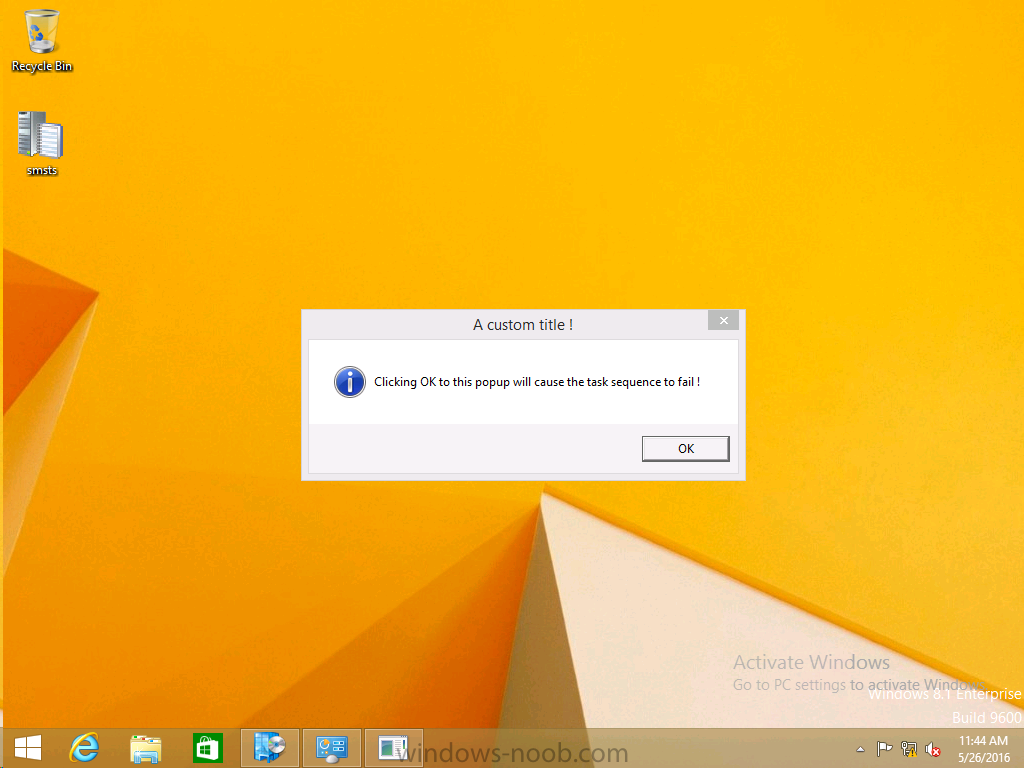
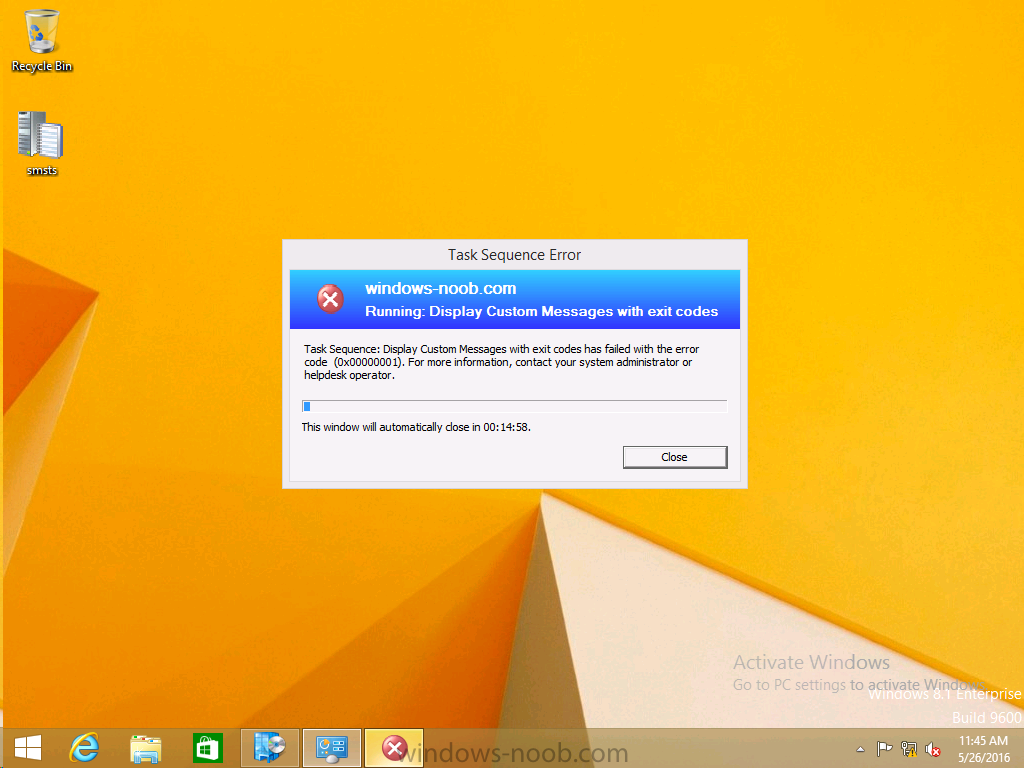
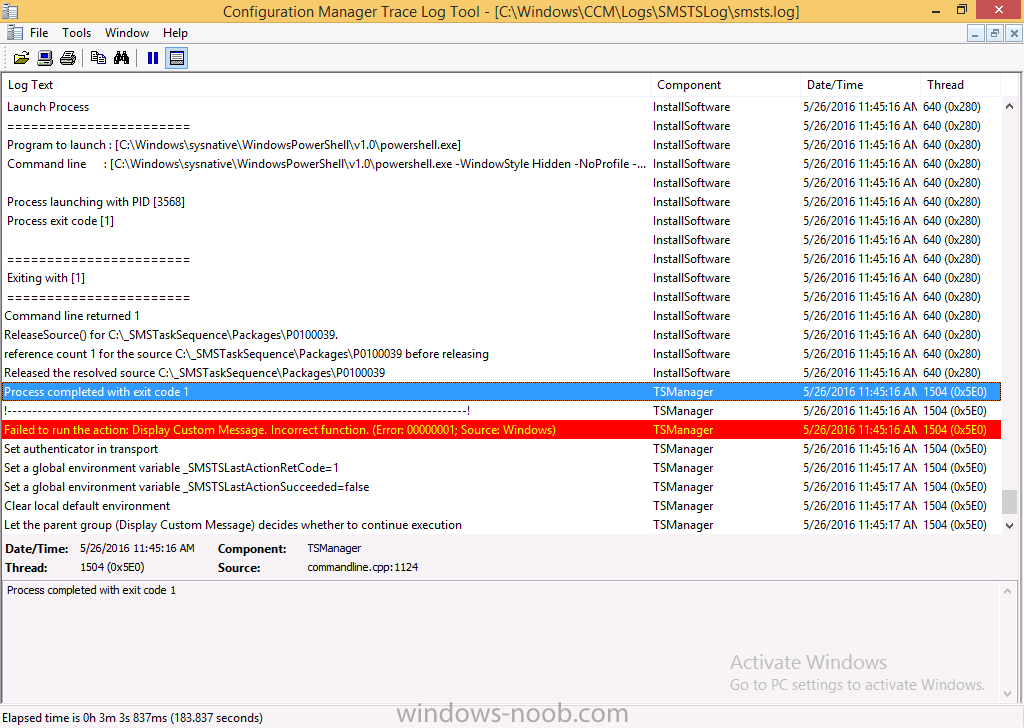
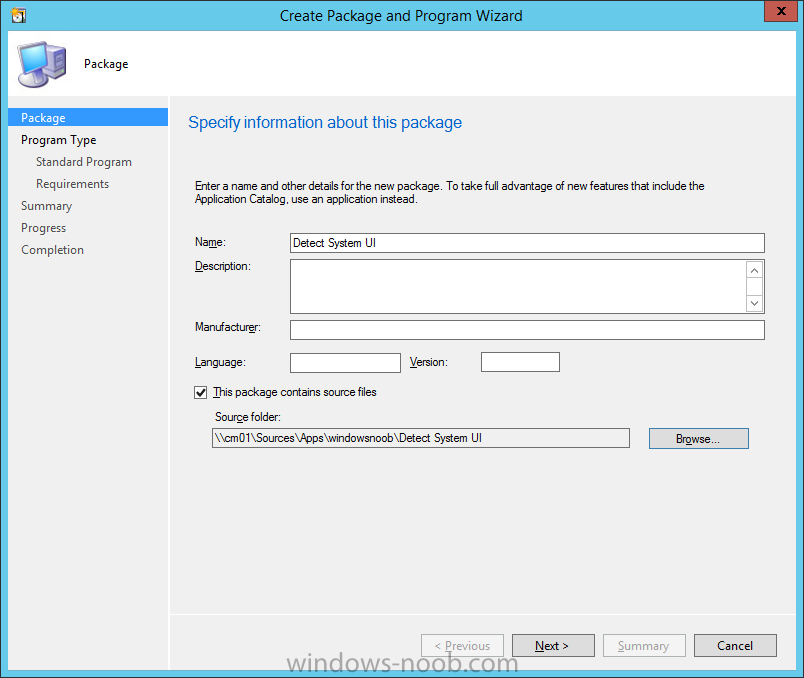
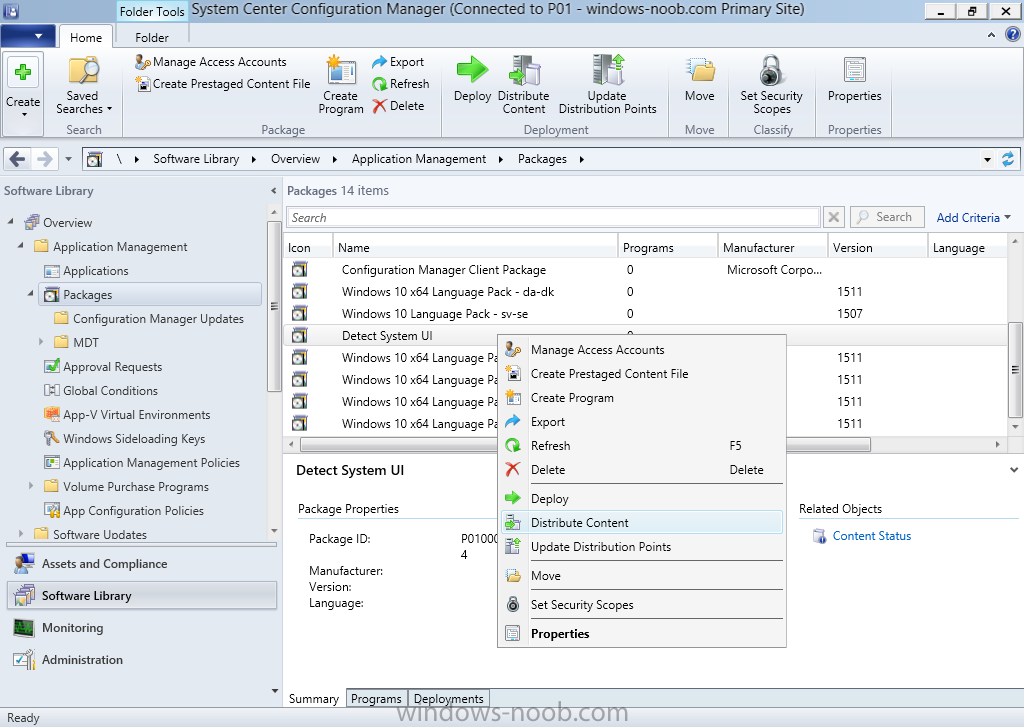
Introduction At the start of this series of step by step guides you installed System Center Configuration Manager (Current Branch), then you configured discovery methods. Next you configured boundaries to get an understanding of how automatic site assignment and content location works. After that you learned how to update ConfigMgr with new features and fixes using a new ability called Updates and Servicing and you learned how to configure ConfigMgr to use Updates and Servicing in one of these two modes: Online mode Offline mode To prepare your environment for Windows 10 servicing (this guide) you learned how to setup Software Updates using an automated method (via a PowerShell script) or manually using the ConfigMgr console. Next you used a PowerShell script to prepare some device collections, then you configured client settings for your enterprise and finally you'll deployed the ConfigMgr client agent using the software updates method which is the least intensive method of deploying the Configuration Manager client agent. As System Center Configuration Manager (current branch) is being delivered as a service now, version 1602 was made available (March 11th, 2016) and you used Updates and Servicing to do an in-place upgrade to that version as explained here. Next you learned about how to use the Upgrade task sequence to upgrade your Windows 7, Windows 8 (and 8.1) and even your Windows 10 devices to a later build of Windows 10. You then learned about the new Windows 10 servicing features which use Servicing Plans in ConfigMgr (Current Branch). Next you integrated MDT 2013 update 2. MDT integration with ConfigMgr is useful as it provides additional functionality for operating system deployment scenarios such as Offline Language Package installation or User Driven Integration (UDI). Next you learned how to deploy Language Packs offline for Windows 10. To assist with Windows 10 servicing and for applying appropriate software updates to your Windows 10 devices, you used PowerShell to add queries to the various Windows 10 collections. Next you took a deeper look at the Windows 10 Upgrade task sequence, and learned one way of dealing with potential upgrade issues. While that method will flag a problem, such as determining the system UI language doesn't match the provided media, it won't allow you to continue with the upgrade. Next you learned how to upgrade the operating system when a language pack was installed, provided that the system UI language is from a 'list' of approved languages that you intend to support. This guide will show you how to display customized messages to a user during a task sequence, and how to set an exit code which could allow you to deliberately fail an action if necessary. All that's required is a few steps to set variables, a PowerShell script, and the serviceUI.exe executable from MDT 2013 Update 2. Step 1. Create a package On your ConfigMgr server, in the sources share, create a folder called Display Custom Message and place the DisplayCustomMessage.ps1 PowerShell script available in the downloads section of this guide, in the folder. Even though you might be deploying an X64 operating system, locate, select and copy the x86 architecture version of ServiceUI.exe from the Sources\OSD\MDT\MDT2013u2\Toolkit\Tools\x86 folder into the Display Custom Message folder as shown below. In the ConfigMgr console, Software Library, select Packages and right click, choose Create Package. Fill in the following details, Choose Do not create a program and then continue through the wizard until completion. Once the package is created, right click the package and choose Distribute Content. Distribute the package to your distribution points. Step 2. Create a custom task sequence In the ConfigMgr console, in Software Library, select Operating Systems and right click on Task Sequences, choose Create Task Sequence. select Create a new custom task sequence give the task sequence a suitable name such as Display Custom Messages with exit codes continue through that wizard until completion. Step 3. Edit the task sequence Right click on the newly created task sequence and choose edit It will appear blank, click on the Add Drop down and add a New Group called Display Custom Message Create a new Set Task Sequence Variable step called Set Title with a Task Sequence Variable called Title, with a suitable value as follows: Create a new Set Task Sequence Variable step called Set Message with a Task Sequence Variable called Message, with a suitable value as follows: Create a new Set Task Sequence Variable step called Set ReturnCode with a Task Sequence Variable called ReturnCode, with a suitable positive value as follows: Click Add and choose Run Command Line, name the step Display Custom Message and paste in the following based on what operating system the client is using: For Windows 8 ServiceUI.exe -process:TSProgressUI.exe %windir%\sysnative\WindowsPowerShell\v1.0\powershell.exe -WindowStyle Hidden -NoProfile -ExecutionPolicy bypass -nologo -file DisplayCustomMessage.ps1 For Windows 10 ServiceUI.exe -process:TSProgressUI.exe %SYSTEMROOT%\System32\WindowsPowerShell\v1.0\powershell.exe -windowstyle hidden -NoProfile -ExecutionPolicy bypass -File DisplayCustomMessage.ps1 For Package, select the Display Custom Message package created above. (screenshot below if for Windows 8 os) Copy the entire group and paste it below the first group Edit the Set Message step as below Edit the Set ReturnCode step, and choose a value that the Options tab on the Display Custom Message step is not going to expect such as 1, this will cause the next step to fail when it returns the return code. Apply your changes and exit the Task Sequence wizard. Step 4. Deploy the task sequence Right Click on the task sequence and choose Deploy Choose a suitable collection and use a purpose of Available. Step 5. Review the capabilities On a client computer that is in the collection that the task sequence was deployed to, open Software Center and select the Display Custom Message with exit codes task sequence. choose Install and after a few moments the first popup message appears ! As the ReturnCode for the first message was set to a value we expected (0 or 3010) it did not fail the task sequence. Click OK to continue... the next message appears, note the different text, and it's hinting towards what will happen Clicking OK will produce the failure Which is OK because we were expecting it, in fact, the ReturnCode we set (1) is listed in the failure message. In a real Production task sequence however, you'd take care of failures and deal with them in a professional way, I just want you to see that we can actually set the ReturnCode via the custom message. To get more proof of that refer to the SMSTS.log file, and you can see that it's setting the ReturnCode to the value we chose result ! Summary Popping up messages to users during a task sequence is sometimes necessary, and when things go wrong, you sometimes need to fail the task sequence or set a ReturnCode to do a planned action. This guide helps you do both of those things dynamically. Related Reading Task sequence steps in System Center Configuration Manager - https://technet.micr...y/mt629396.aspx If you'd like to send a notification message to users in Intune in Azure, try the following guide. Downloads You can download a Microsoft Word copy of this guide here dated 2016/05/26 How can I display custom messages to users during a task sequence in SCCM Current Branch.zip You can download the PowerShell script used above here: DisplayCustomMessage.zip\
-
sounds like this problem
-
yes sorry, see this post
-

Dynamic Task Sequence selection frontend
anyweb replied to Bav's question in Frontends, HTA's and Web Services
you can use ad credentials with the adsi winpe plugin from Johan Arwidmark, please share the solution you come up with so others can benefit. -

Dynamic Task Sequence selection frontend
anyweb replied to Bav's question in Frontends, HTA's and Web Services
you could convert my devel mode task sequence logic to do that -
if you want to deploy and manage Windows 10 then you should move to SCCM version 1511 (Current Branch) as soon as possible (and then upgrade to 1602). The current release of System Center Configuration Manager 2012 R2 can only deploy and manage Windows 10 up to version 1511 and not beyond (i.e. Redstone)
-
what device are you trying to pxe boot with ? is it a virtual machine or a real computer ? did you add network drivers for it to the boot image ? it doesn't look like it
- 1 reply
-
- SCCM PXE issues
- sccm2012
-
(and 1 more)
Tagged with:
-
i've seen something similar before, possibly due to hash errors on the package, can you zip up some logs and we take a look...
-
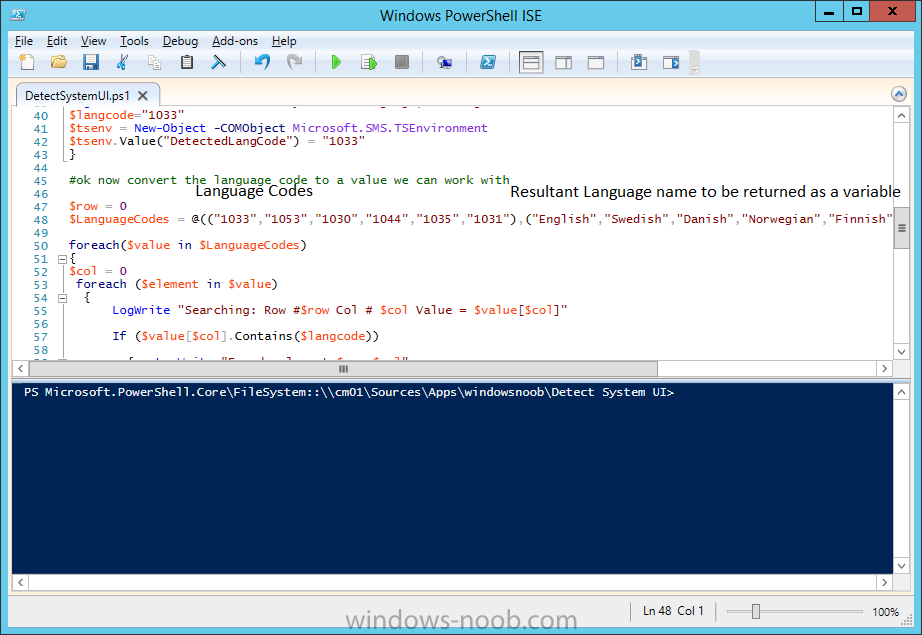
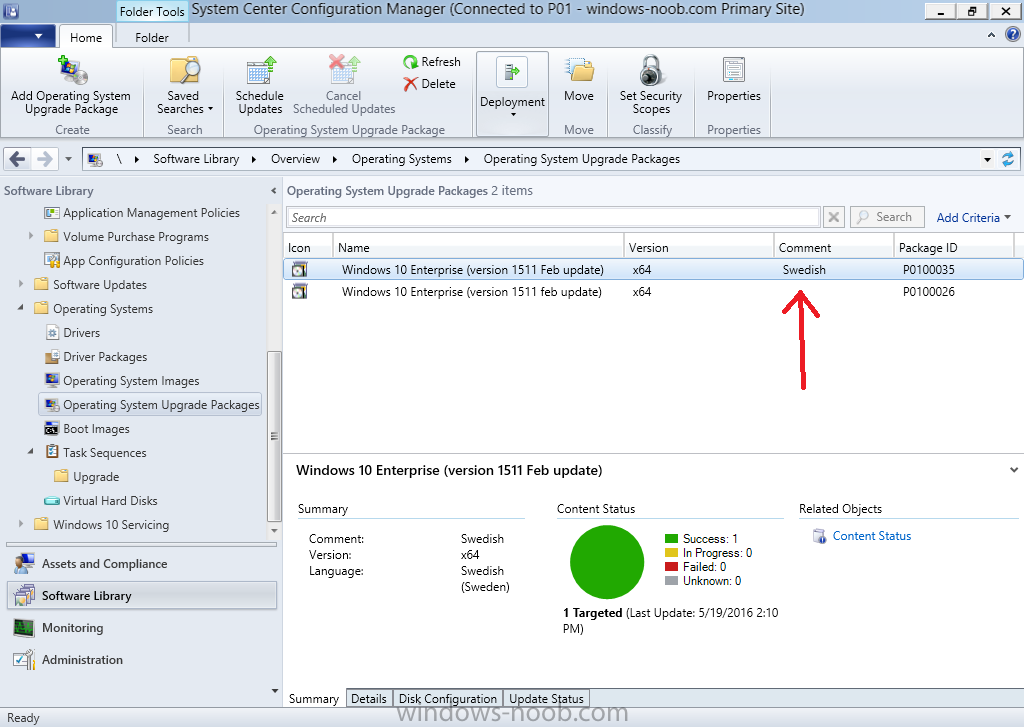
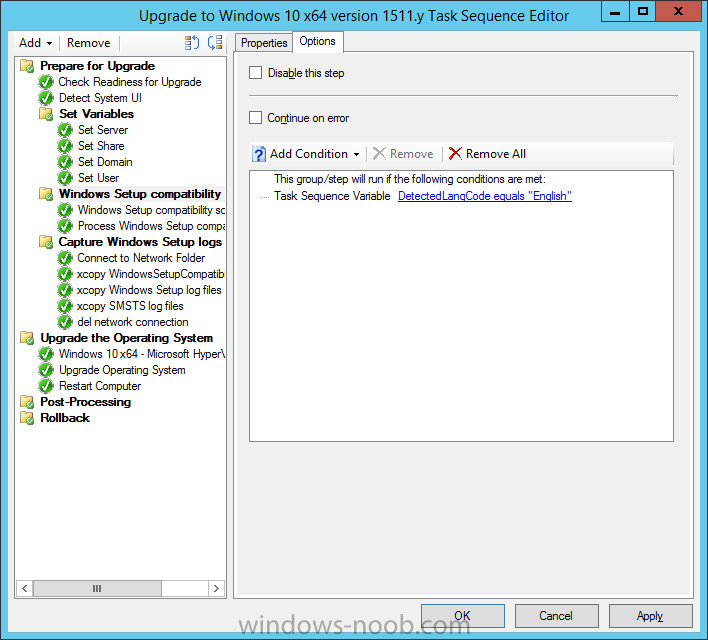
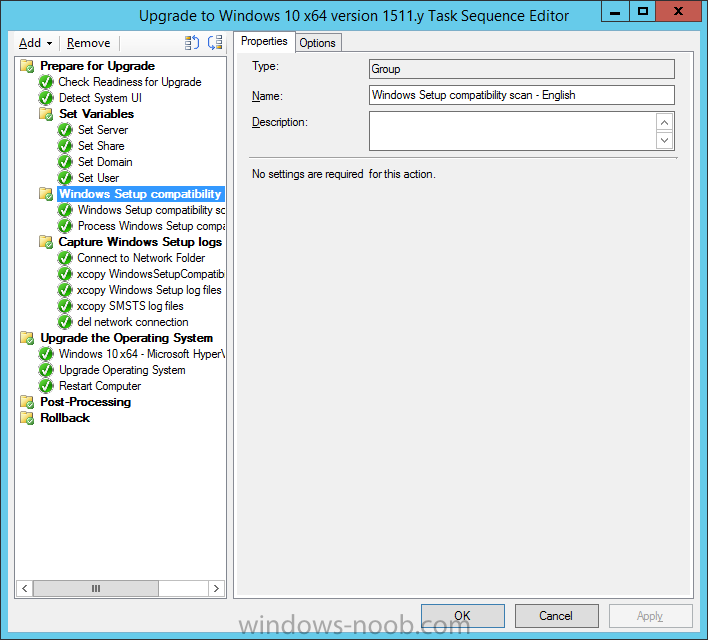
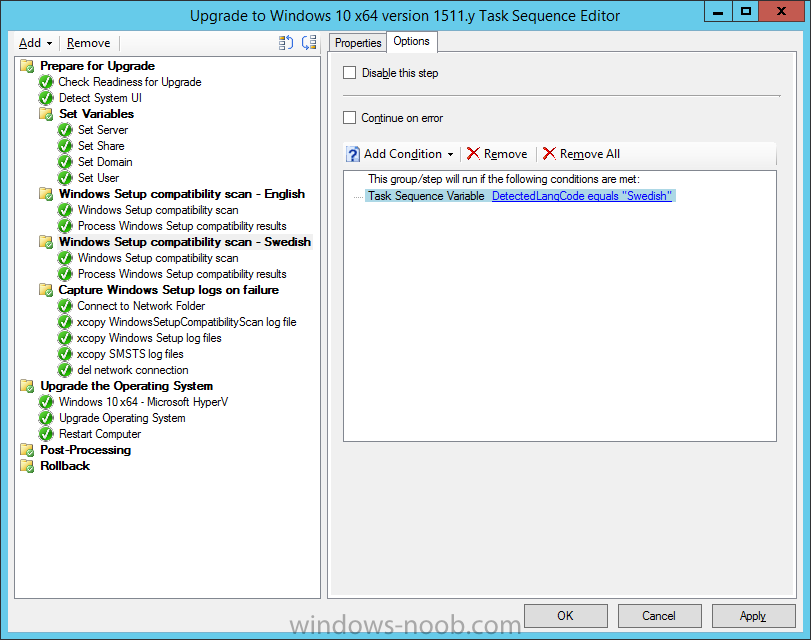
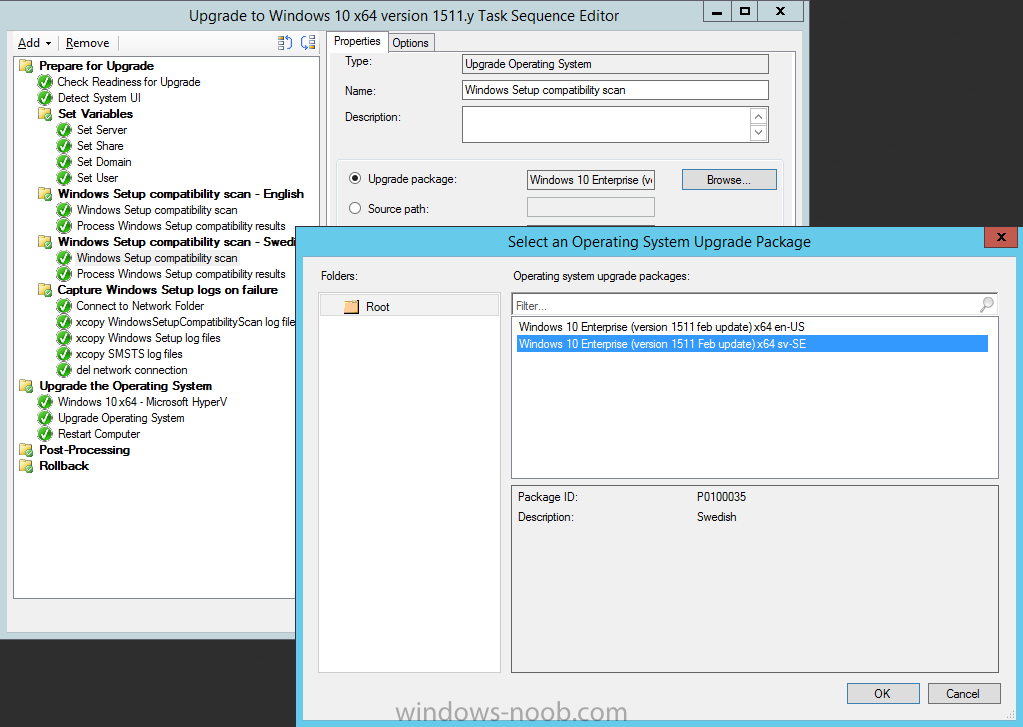
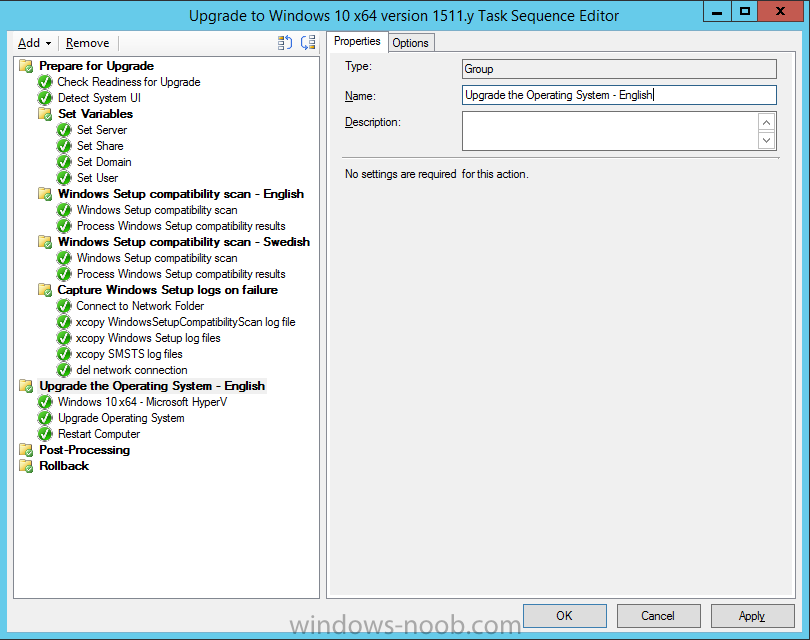
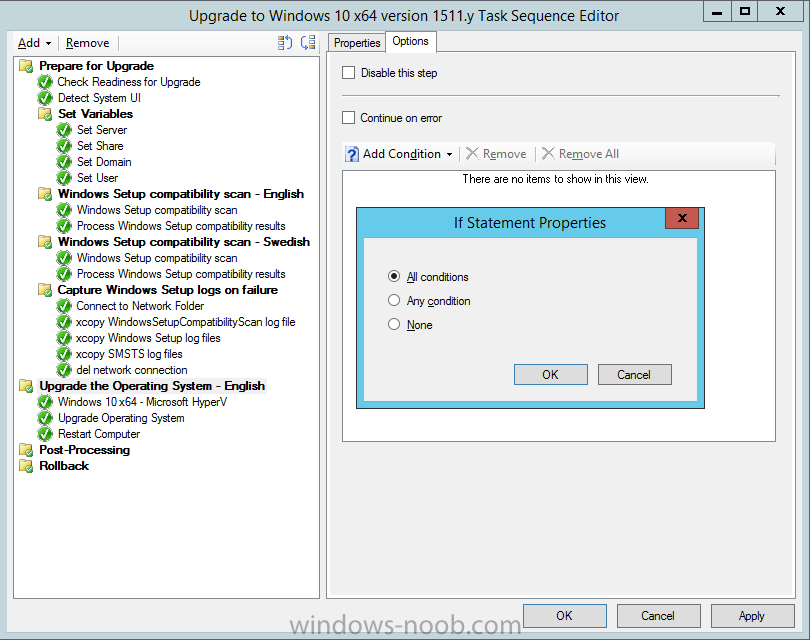
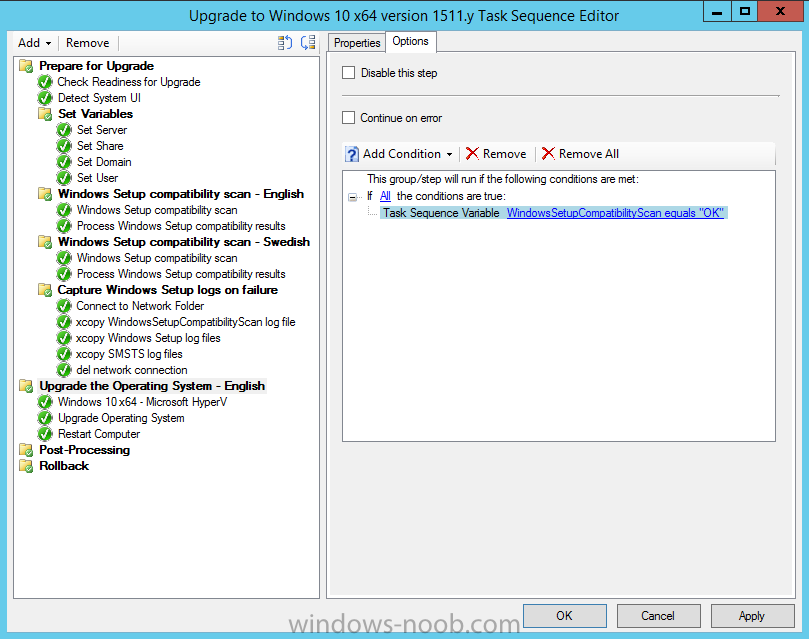
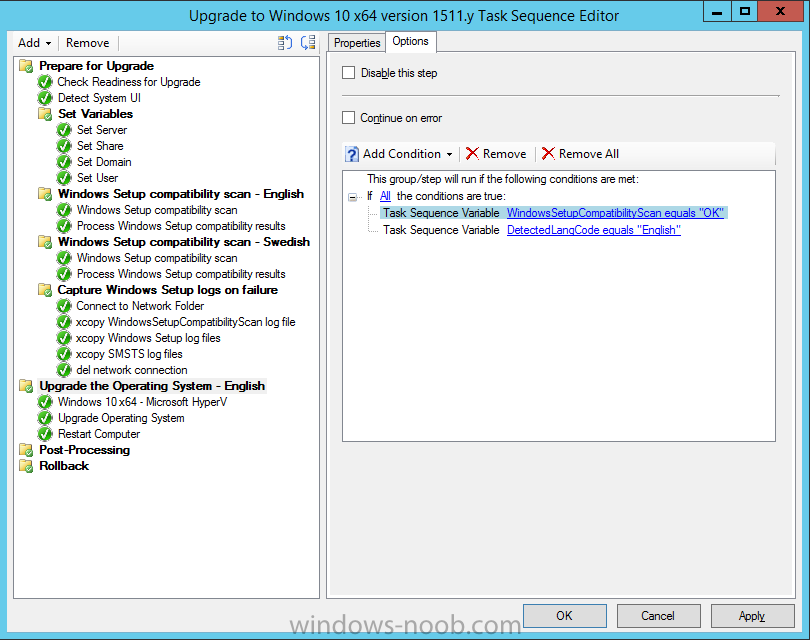
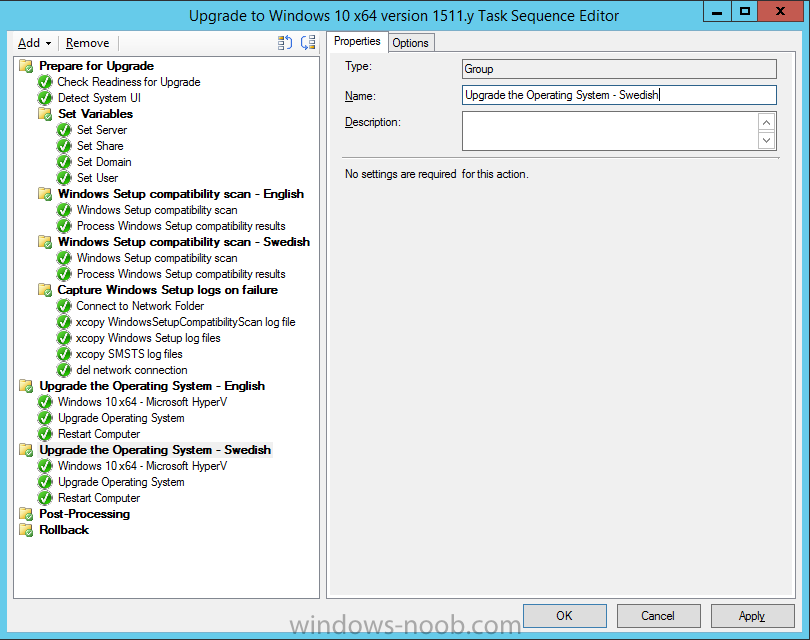
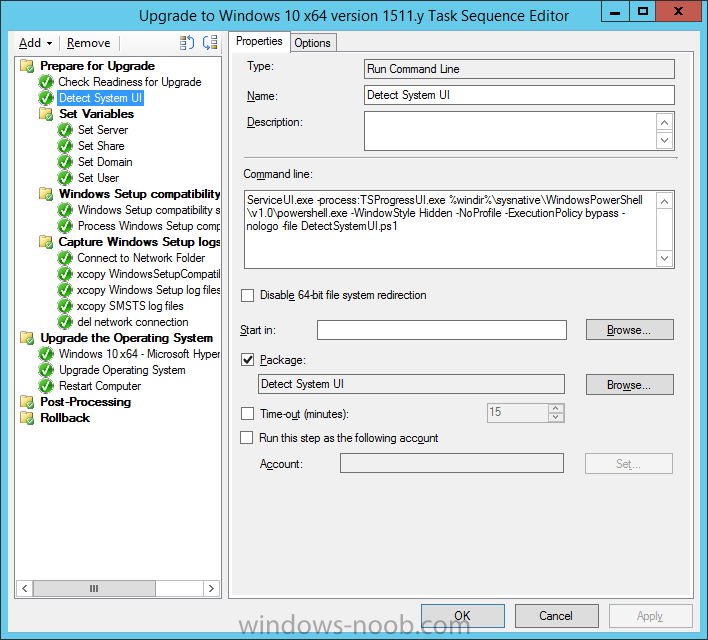
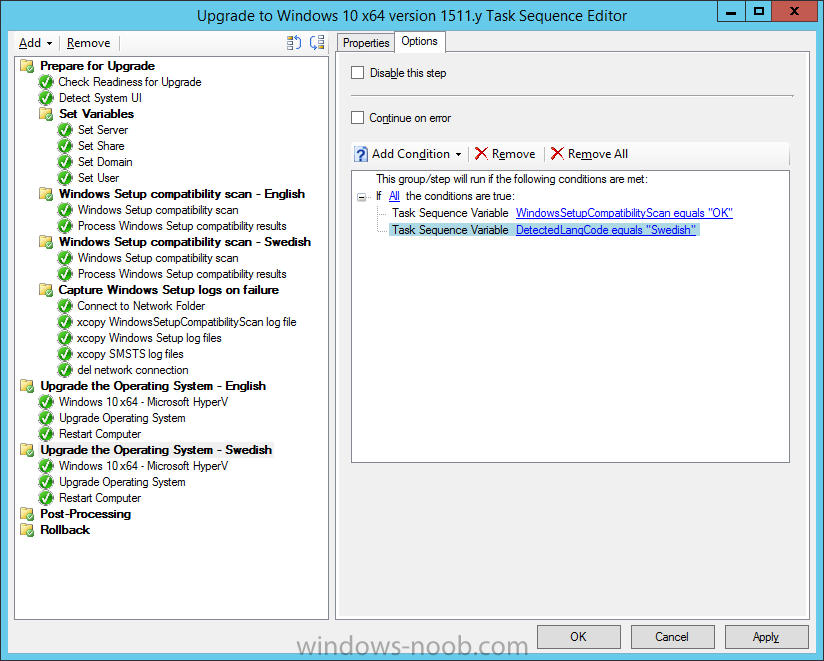
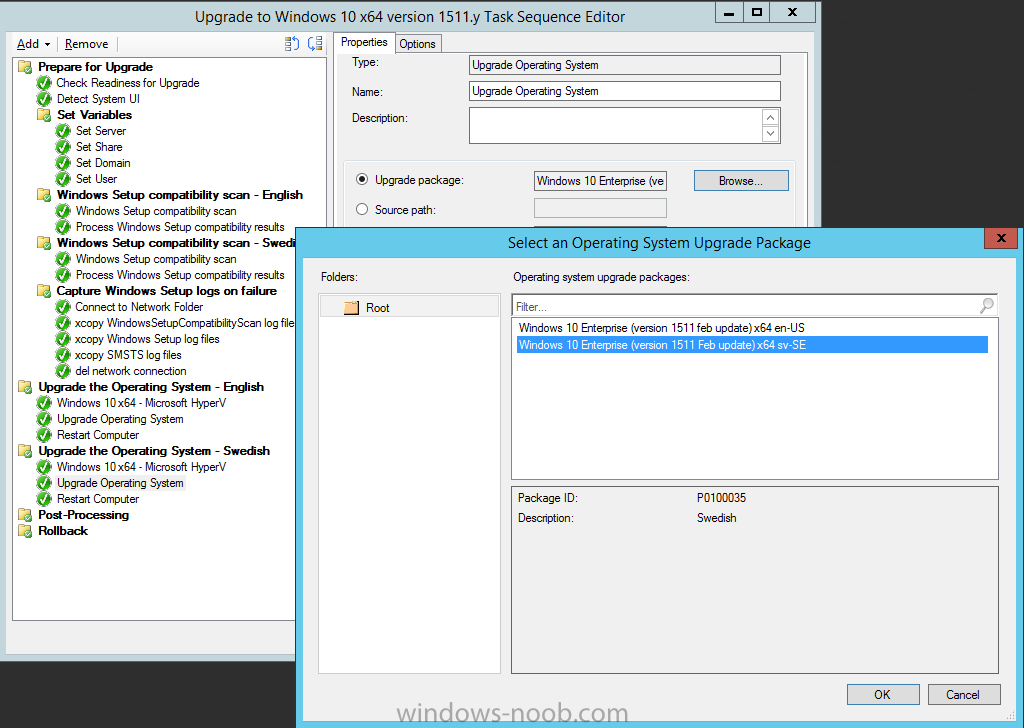
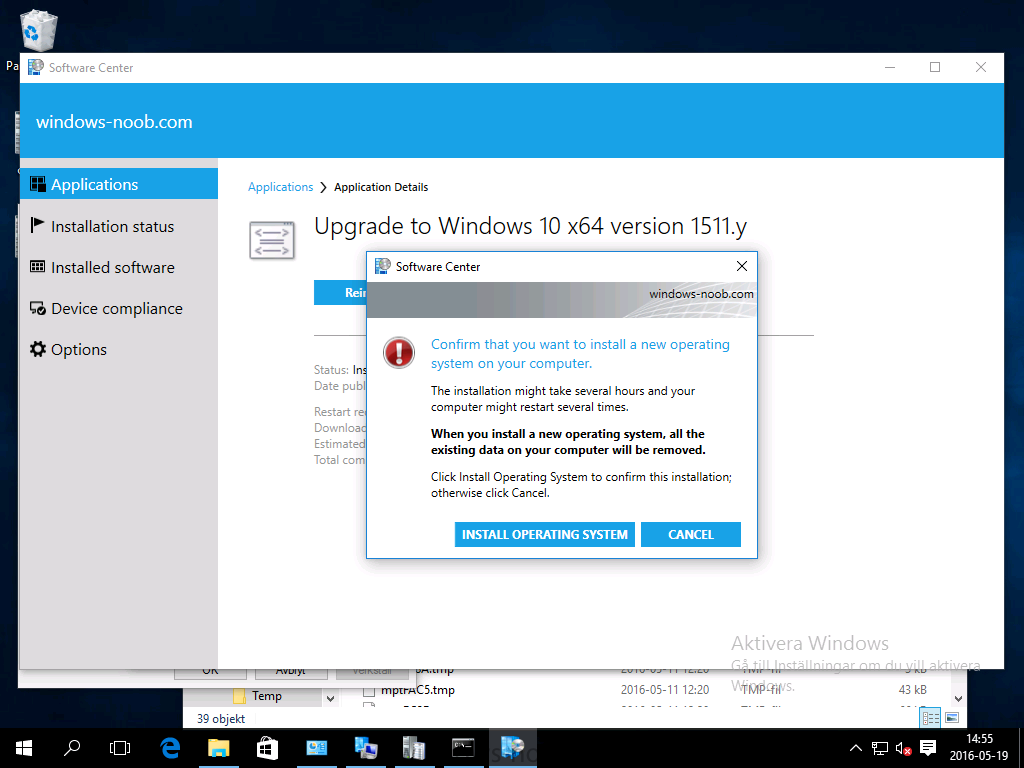
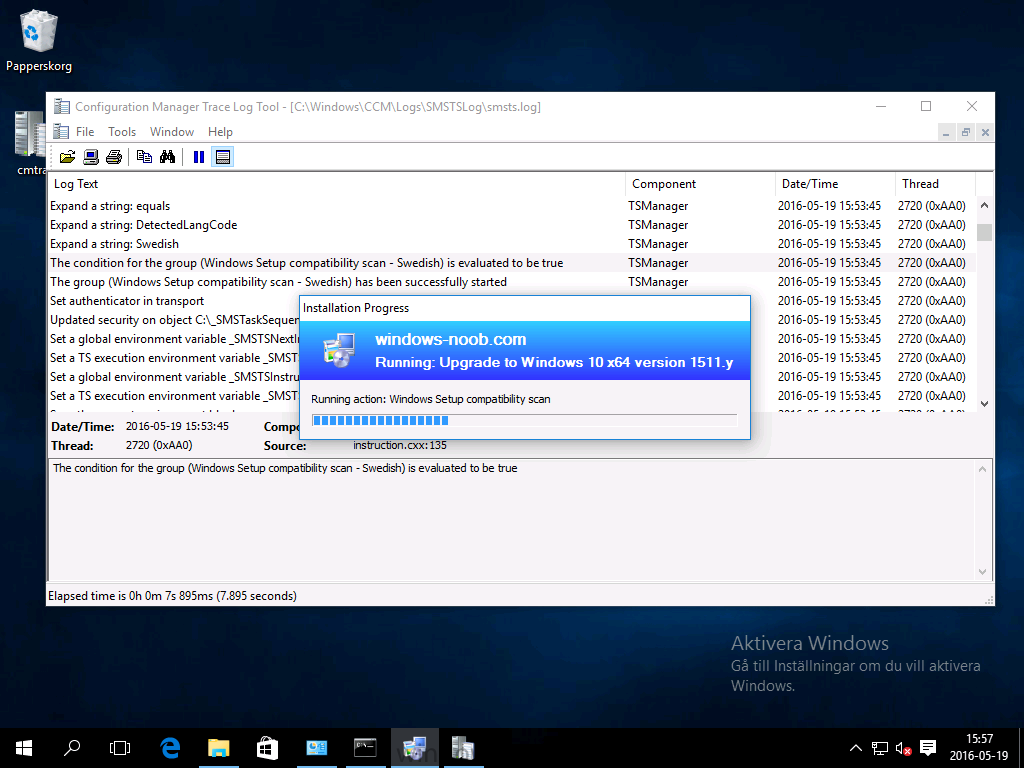
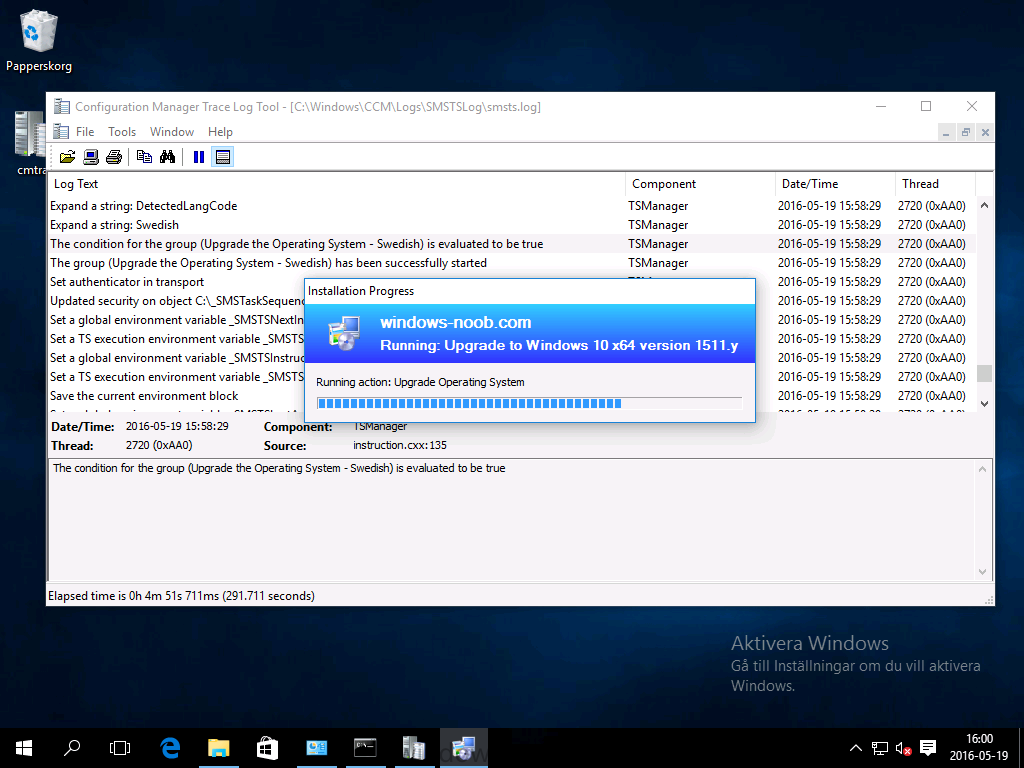
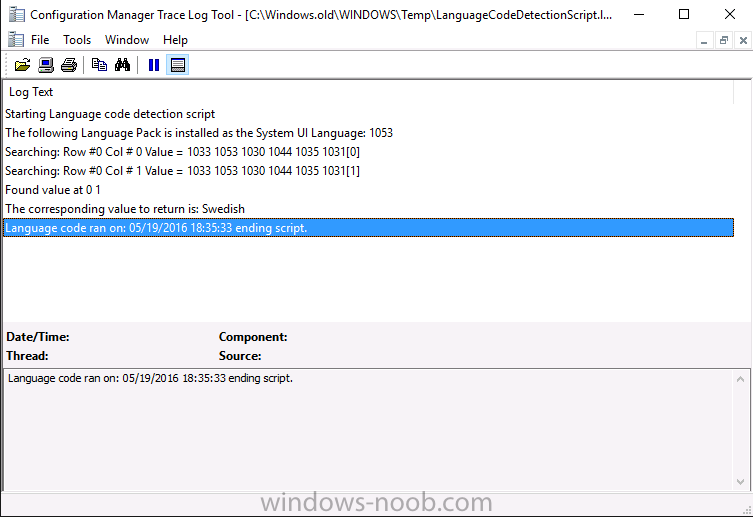
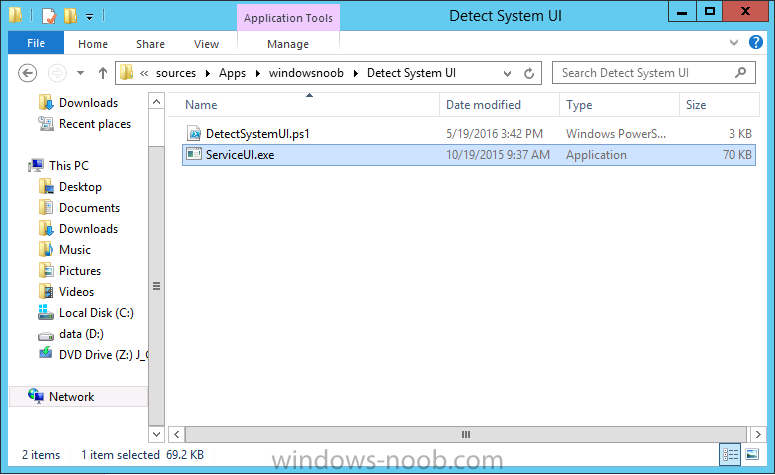
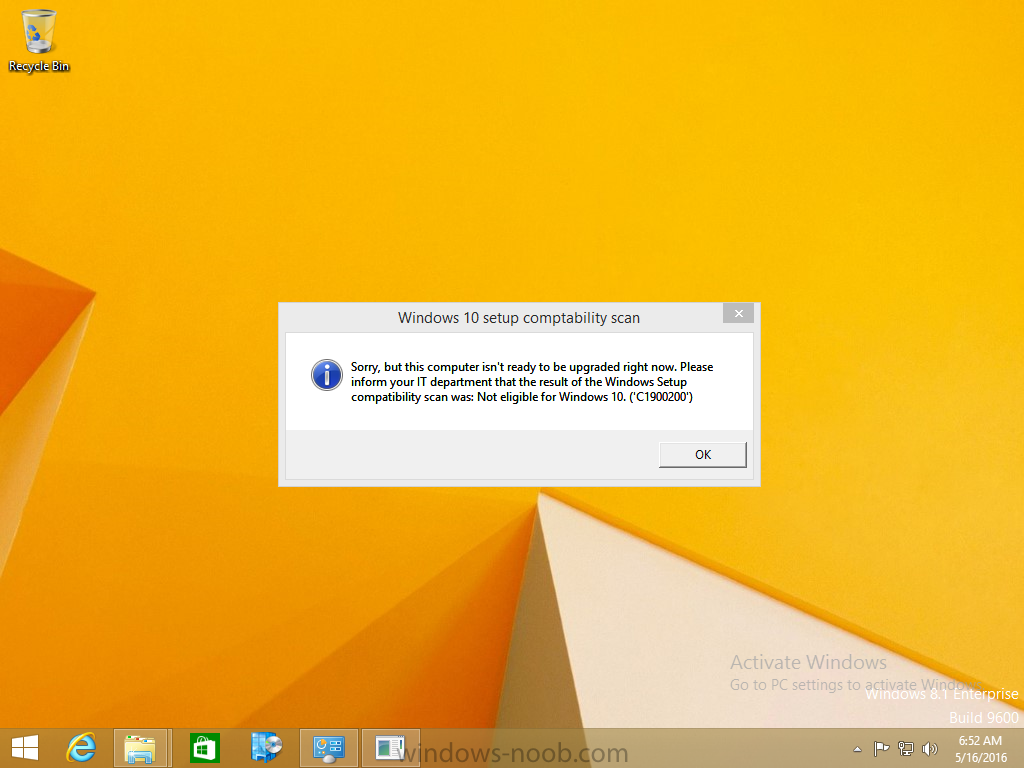
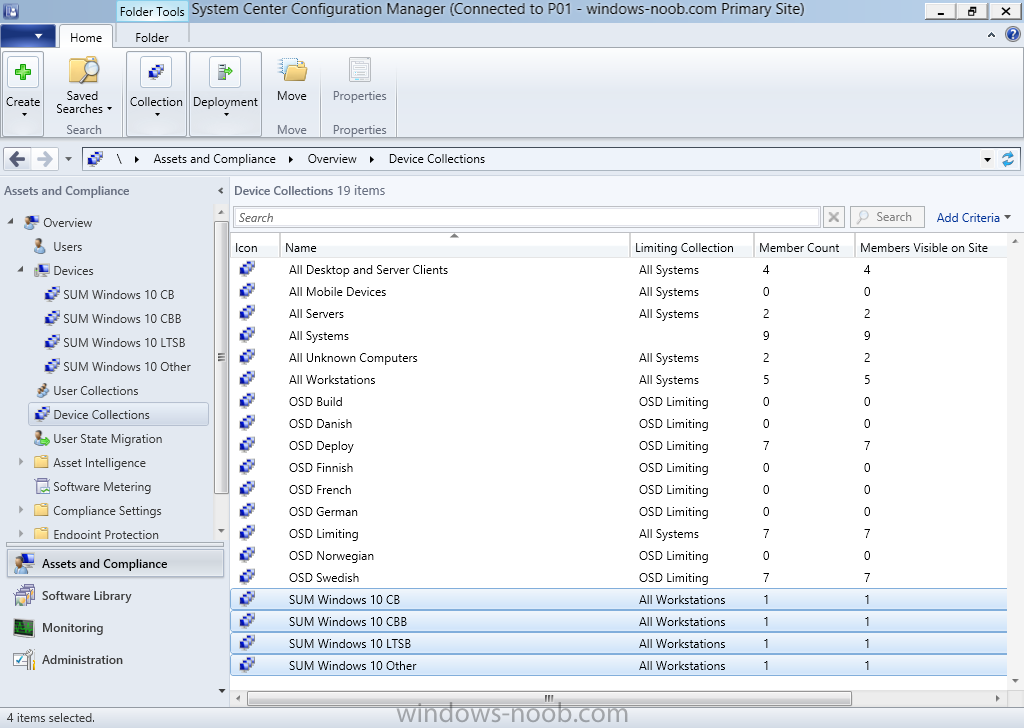
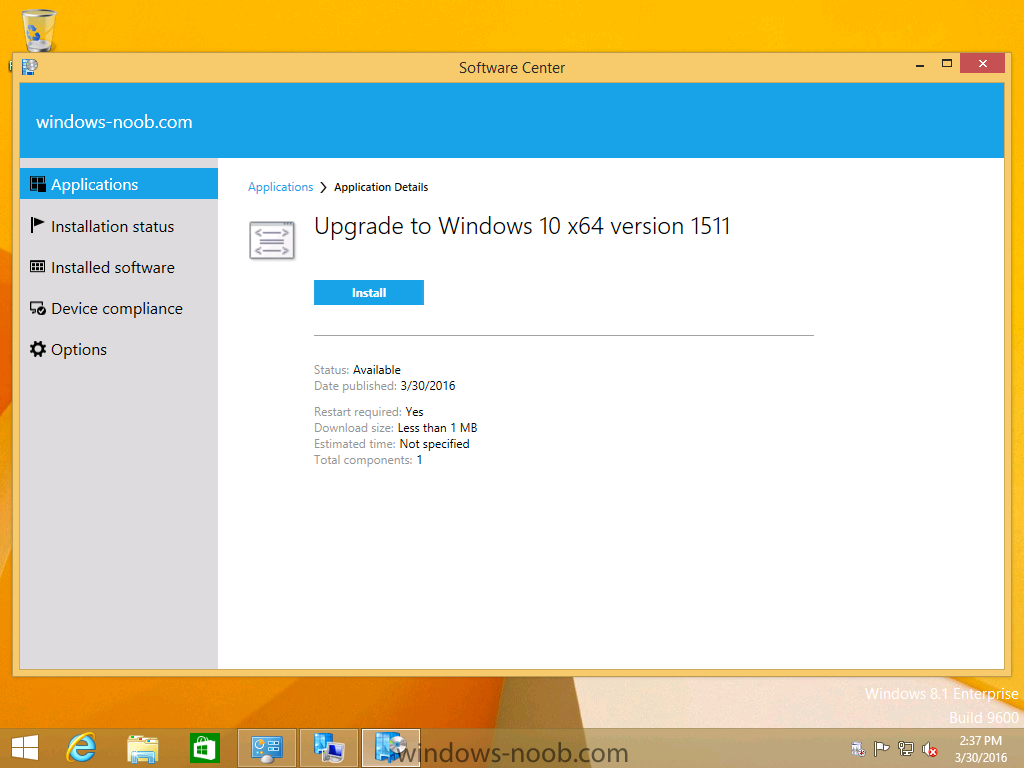
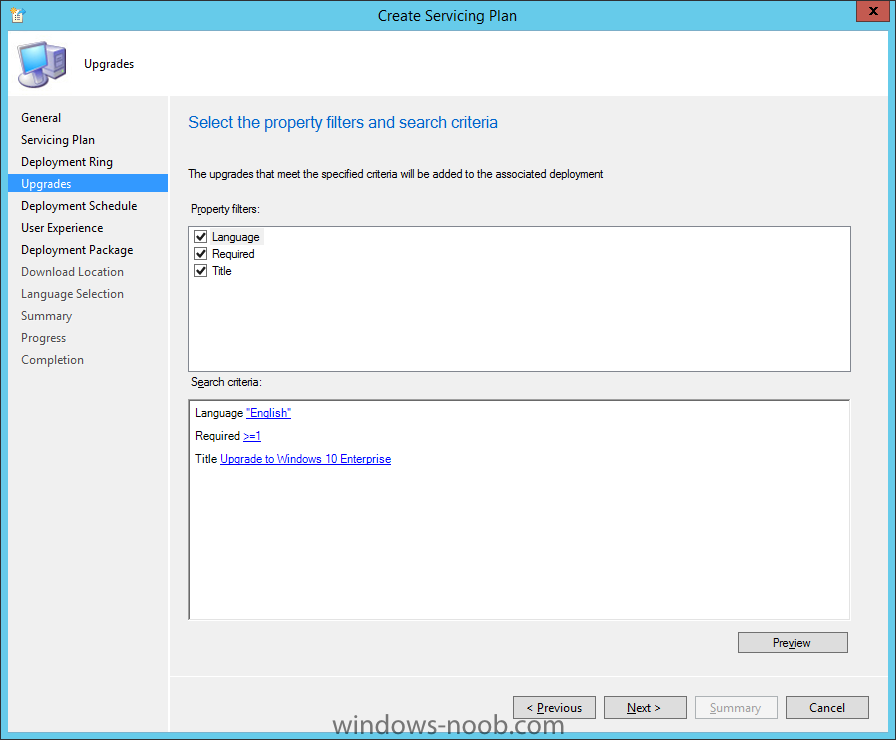
Introduction At the start of this series of step by step guides you installed System Center Configuration Manager (Current Branch), then you configured discovery methods. Next you configured boundaries to get an understanding of how automatic site assignment and content location works. After that you learned how to update ConfigMgr with new features and fixes using a new ability called Updates and Servicing and you learned how to configure ConfigMgr to use Updates and Servicing in one of these two modes: Online mode Offline mode To prepare your environment for Windows 10 servicing (this guide) you learned how to setup Software Updates using an automated method (via a PowerShell script) or manually using the ConfigMgr console. Next you used a PowerShell script to prepare some device collections, then you configured client settings for your enterprise and finally you'll deployed the ConfigMgr client agent using the software updates method which is the least intensive method of deploying the Configuration Manager client agent. As System Center Configuration Manager (current branch) is being delivered as a service now, version 1602 was made available (March 11th, 2016) and you used Updates and Servicing to do an in-place upgrade to that version as explained here. Next you learned about how to use the Upgrade task sequence to upgrade your Windows 7, Windows 8 (and 8.1) and even your Windows 10 devices to a later build of Windows 10. You then learned about the new Windows 10 servicing features which use Servicing Plans in ConfigMgr (Current Branch). Next you integrated MDT 2013 update 2. MDT integration with ConfigMgr is useful as it provides additional functionality for operating system deployment scenarios such as Offline Language Package installation or User Driven Integration (UDI). Next you learned how to deploy Language Packs offline for Windows 10. To assist with Windows 10 servicing and for applying appropriate software updates to your Windows 10 devices, you used PowerShell to add queries to the various Windows 10 collections. Next you took a deeper look at the Windows 10 Upgrade task sequence, and learned one way of dealing with potential upgrade issues. While that method will flag a problem, such as determining the system UI language doesn't match the provided media, it won't allow you to continue with the upgrade. This post will show you one method to upgrade the operating system, provided that the system UI language is from a 'list' of approved languages that you intend to support. This method uses a PowerShell script that runs the below query to check for the language installed ([wmi]"root\cimv2:win32_OperatingSystem=@").OSLanguage It then compares that result to your approved list of language codes (and resulting names, eg: 1033=English). The section of the PowerShell script that you can edit to expand/reduce this functionality is highlighted below. Just make sure that the Language Code listed on the left, matches the Language Variable name that you want to return to the task sequence as a variable, a full list of these potential values is here in the Language Codes section. Once the script has run, it will set a variable that can be checked for in the task sequence, the variable is called DetectedLangCode. Note: There are at least three methods dealing with Language Packs installed in Windows 10 for the Upgrade Task Sequence, this is one method. If i get time i'll blog the other methods too (however they are less supported than this method). The downside to this method is that you need one media step for each language installed (including an additional step if using the Windows setup compatibility scan). Step 1. Create a package On your ConfigMgr server, in the sources share, create a folder called Detect System UI and place the DetectSystemUI.ps1 PowerShell script in the folder. Even though you are deploying an X64 operating system, locate, select and copy ServiceUI.exe from the Sources\OSD\MDT\MDT2013u2\Toolkit\Tools\x86 folder into the Detect System UI folder as shown below. In the ConfigMgr console, Software Library, select Packages and right click, choose Create Package. Fill in the following details, Choose Do not create a program and then continue through the wizard until completion. Once the package is created, right click the package and choose Distribute Content. Distribute the package to your distribution points. Step 2. Create Windows 10 Upgrade Packages for the languages you intend to support. Logon to your Microsoft Volume License site and download the correct version of the Windows 10 1511 (Feb 2016 update) media that is available in each language that you intend to support, so if you have 10 languages to support, you need all 10 media isos. Once downloaded, add the media as a new Windows 10 Upgrade Package into ConfigMgr. To add Windows 10 version 1511 as an operating system upgrade package do as follows: In the Configuration Manager console, click Software Library and expand Operating Systems then click Operating System upgrade packages. Right click on Operating System upgrade packages and choose Add Operating System upgrade package. When the wizard appears fill in the UNC path to the media and click on next, make sure to fill in a comment to note the language of the media. Once done creating the package update it to your Distribution Points. Rinse and repeat for each language you intend to support. Step 3. Edit the task sequence to determine system UI language By default, after creating an upgrade task sequence you'll have one language media added (probably English). However, if you deploy Windows 10 language packs offline or install the language pack in such as way as to change the UILanguage in the unattend.xml, the installed language pack (for example Swedish) will be set as the system UI language even if the base operating system language was English. The PowerShell script at the bottom of this guide can be run to set a variable at the start of the task sequence and the task sequence will utilize this variable to allow the process to continue with the Upgrade task sequence without failing over. In this guide you will use the Upgrade task sequence created in the previous guide. In the Prepare for Upgrade group select the Check Readiness for upgrade step, click Add and choose Run Command Line, name the step Detect System UI and paste in the following: ServiceUI.exe -process:TSProgressUI.exe %windir%\sysnative\WindowsPowerShell\v1.0\powershell.exe -WindowStyle Hidden -NoProfile -ExecutionPolicy bypass -nologo -file DetectSystemUI.ps1 For Package, select the Detect System UI package created above. Step 4. Edit the task sequence to set the Windows Setup Compatibility scan languages Next, navigate to the Windows Setup compatibility scan group and Change the name of the group from Windows Setup compatibility scan to Windows Setup compatibility scan - English Next, select the options tab. Add a task sequence variable check for DetectedLangCode = English copy the group (right click copy, right click paste) and rename the copied group to Windows Setup compatibility scan - Swedish (or whatever language you intend to add support for) Click on the Options tab and change the variable from English to Swedish. select the Windows Setup compatibility scan step and change the media to point to the matching language that this group will support (eg: Swedish). Repeat the above for each language you intend to support. Step 5. Edit the task sequence to set the Upgrade the Operating System languages Next, select the Upgrade the Operating System group and rename it to Upgrade the Operating System - English Next, select the options tab. Remove the current variables added and then click on Add Condition, If statement, then All Conditions. next click on Add Condition, and add a set task sequence variable WindowsSetupCompatibilityScan = OK and...again click on Add Condition, and add a set task sequence variable DetectedLangCode = English copy the group (right click copy, right click paste) and rename the copied group to Upgrade the Operating System - Swedish (or whatever language you intend to add support for) Click on the Options tab and change the DetectedLangCode variable from English to the language you intend to support. Next select the Upgrade Operating System step and click on browse to change the media from English to the language you intend to support continue doing the above for each language you intend to support, apply the changes and close the task sequence editor. Step 6. Review the results On a computer that is running a language that was added as a language pack and which changed the System UI to match that language, run the Upgrade to Windows 10 task sequence. In this example we are attempting to upgrade a Swedish Windows 10 operating system to the next version of Windows 10. As you can see the login screen is in Swedish. In Software Center, select the task sequence and choose Install (or reinstall if needed), click on Install Operating System when prompted If you want to monitor the event live, then use CMTrace to monitor C:\Windows\CCM\Logs\SMSTSLOG\smsts.log you should see that it correctly identifies the language for the Windows Setup Compatibility scan group and indeed the Upgrade Operating System - Swedish should kick off without a hitch, and off it goes... Note: The log file generated by this script is stored in C:\Windows\Temp and contains info about the detected Language Code and the variable that DetectedLangCode will be set to. The name of the log file is LanguageCodeDetectionScript.log after a successful upgrade, Job done ! Summary In this guide you've applied steps and groups to the Upgrade Task Sequence to detect the System UI language, and apply the correct media where needed, both for the Windows Setup Compatibility scan and for the Upgrade Operating System steps. Dealing with different System UI languages in Windows 10 upgrade scenarios using the Upgrade task sequence isn't straight forward but at least there's way's to solve the problem. Related Reading A deeper look at the Upgrade task sequence in System Center Configuration Manager (Current Branch) - https://www.windows-noob.com/forums/topic/14118-a-deeper-look-at-the-upgrade-task-sequence-in-system-center-configuration-manager-current-branch/ How can I install Windows 10 language packs offline with an MDT Integrated Task Sequence in System Center Configuration Manager (Current Branch) - https://www.windows-noob.com/forums/topic/14059-how-can-i-install-windows-10-language-packs-offline-with-an-mdt-integrated-task-sequence-in-system-center-configuration-manager-current-branch/ Appendix F - Country/Region and Language Codes - https://technet.microsoft.com/en-us/library/dd346950.aspx Windows 10 MUI challenge - https://rzander.azurewebsites.net/how-to-change-the-welcome-screen-language-in-win10/ Downloads You can download a Microsoft Word copy of this guide here dated 2016/05/19 How can I detect the system ui in an upgrade task sequence.zip You can download the PowerShell script used above here. DetectSystemUI.zip
-
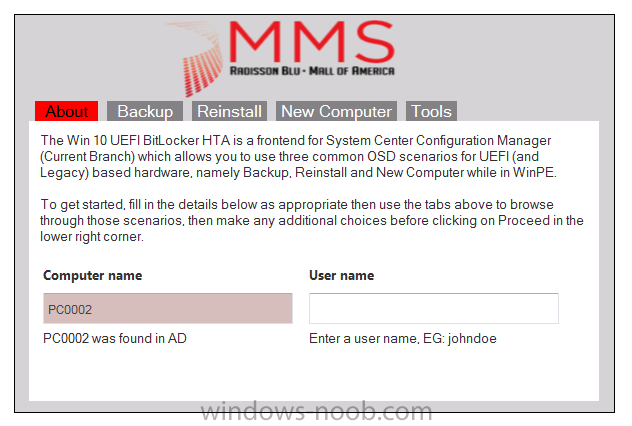
here are a bunch of links which cover many of the things i talked about in the last two days @ MMS: Introducing the Windows 10 UEFI BitLocker Frontend for System Center Configuration Manager (Current Branch) - https://www.niallbrady.com/2016/05/17/introducing-the-windows-10-uefi-bitlocker-frontend-for-system-center-configuration-manager-current-branch/ A deeper look at the Upgrade task sequence in System Center Configuration Manager (Current Branch) - https://www.niallbrady.com/2016/05/15/a-deeper-look-at-the-upgrade-task-sequence-in-system-center-configuration-manager-current-branch/ How can I use PowerShell to populate Windows 10 CB, CBB, LTSB and Insider Preview collections in System Center Configuration Manager (Current Branch) - https://www.niallbrady.com/2016/05/13/how-can-i-use-powershell-to-populate-windows-10-cb-cbb-ltsb-and-insider-preview-collections-in-system-center-configuration-manager-current-branch/ How can I use the Upgrade Task Sequence in System Center Configuration Manager (current branch) ? https://www.windows-noob.com/forums/topic/13917-how-can-i-use-the-upgrade-task-sequence-in-system-center-configuration-manager-current-branch/ How can I use servicing plans in System Center Configuration Manager (Current Branch) to upgrade Windows 10 devices ? - https://www.windows-noob.com/forums/topic/13968-how-can-i-use-servicing-plans-in-system-center-configuration-manager-current-branch-to-upgrade-windows-10-devices/ How can I use the Upgrade Task sequence to deal with languages in System Center Configuration Manager (Current Branch) - https://www.windows-noob.com/forums/topic/14141-how-can-i-use-the-upgrade-task-sequence-to-deal-with-languages-in-system-center-configuration-manager-current-branch/ cheers niall